Importance of Security in CI/CD Pipelines
Security is paramount in continuous integration and continuous delivery (CI/CD) pipelines, as vulnerabilities can lead to severe consequences, including data breaches and financial loss. Ensuring security in CI/CD pipelines helps organizations maintain customer trust and protect their business reputation.
The Role of Security-First Pipelines in Empowering Organizations
By implementing security-first pipelines, organizations can proactively address potential risks in their development processes, leading to more reliable and secure applications. This approach fosters a culture of security and enables collaboration between development, operations, and security teams.
Overview of the Blog Content
This blog will explore the various components and challenges of CI/CD pipelines, discuss the integration of security measures, and share best practices to help organizations strengthen their pipeline security.
Understanding CI/CD Pipelines
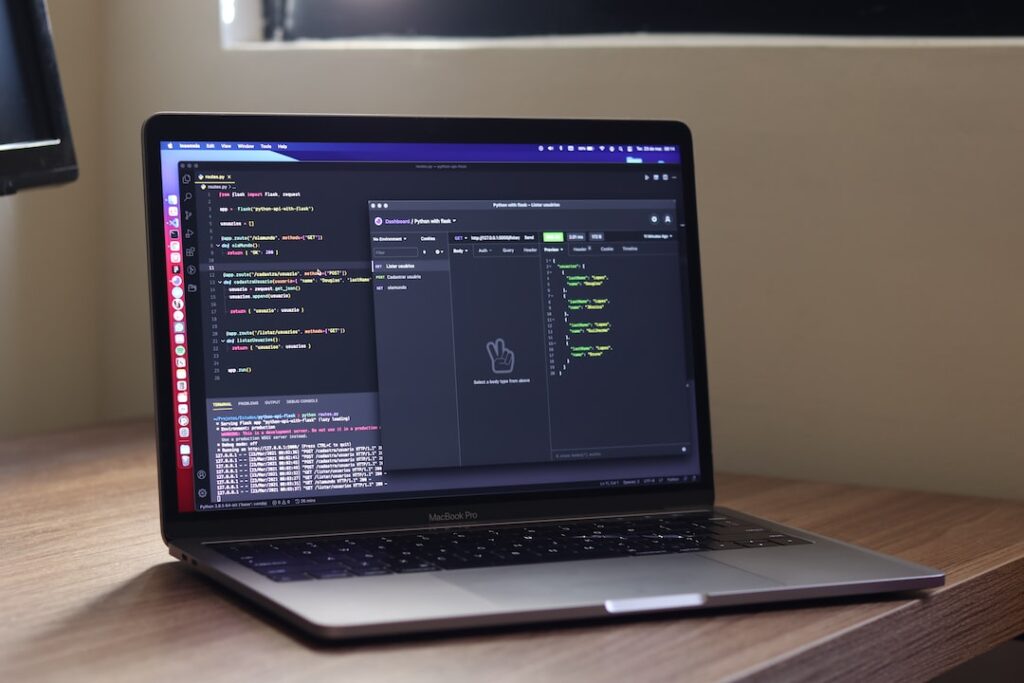
Continuous Integration (CI) and Continuous Delivery (CD) are crucial concepts in modern software development. CI focuses on integrating code changes frequently, allowing teams to detect issues early in the development process. CD, on the other hand, ensures that software updates are delivered to end-users quickly and efficiently.
Various components within a CI/CD pipeline can be at risk, including source-code repositories, build servers and workers, artifact repositories, and deployment environments. Securing these components is essential to prevent vulnerabilities that could lead to data breaches and other security incidents.
Ensuring security in CI/CD pipelines can be challenging. Some of the common challenges include the complexity of the pipeline, the speed at which new code is pushed, the need for automation, and the management of access control. Addressing these challenges requires a comprehensive approach that incorporates security measures throughout the development process, from source code management to deployment.
Integrating Security in the CI/CD Process
DevSecOps is an approach that integrates security practices into the development workflow, addressing security challenges in software application delivery. This concept emphasizes the need for collaboration between development, operations, and security teams, fostering a proactive and security-centric mindset.
Shifting security left in the development workflow means incorporating security measures early in the process, allowing for the detection and mitigation of vulnerabilities before they become critical. This approach reduces the likelihood of security incidents and helps organizations maintain a secure and reliable development process.
Incorporating security controls throughout the pipeline is crucial for safeguarding CI/CD processes. This includes implementing security measures in source code management, build and test automation, artifact storage, and deployment environments. By integrating security at every stage of the pipeline, organizations can ensure a comprehensive and robust security posture, leading to more secure applications and infrastructure.
Automating Security in CI/CD Pipelines
Automation plays a significant role in minimizing human error and vulnerabilities within CI/CD pipelines. By automating security tasks, organizations can reduce the risk of misconfigurations and ensure consistent security practices across the development process.
Routine scanning, security testing, monitoring, and auditing are essential for maintaining a secure pipeline. This includes scanning source code for potential vulnerabilities, examining containers for security issues, and monitoring infrastructure for any signs of compromise. Implementing these measures allows organizations to proactively detect and address security risks in their CI/CD pipelines.
Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) are two complementary approaches to identify vulnerabilities in applications. SAST analyzes source code for security flaws, while DAST simulates attacks on running applications to identify potential weaknesses. Using both methods ensures a comprehensive security assessment of applications throughout the development process.
Leveraging security tools like SonarQube and Checkmarx can help organizations automate security testing and integrate security measures seamlessly into their CI/CD pipelines. These tools provide valuable insights into potential vulnerabilities and help development teams prioritize and address security issues throughout the development lifecycle.
Best Practices for CI/CD Security
Implementing best practices for CI/CD security helps organizations prevent vulnerabilities and create more secure applications. Some of these best practices include:
Automating security scans: Integrating automated security scanning tools into the CI/CD pipeline helps identify vulnerabilities early in the development process, reducing the risk of security incidents.
Managing secrets effectively: Ensuring that sensitive information, such as API keys and passwords, is securely stored and accessed can prevent unauthorized access and data breaches.
Using immutable infrastructure: Employing an infrastructure that cannot be changed after deployment ensures consistency across environments and minimizes the risk of configuration drift.
Regularly updating and patching: Keeping software components up-to-date and applying security patches promptly can help protect against known vulnerabilities and potential exploits.
Implementing role-based access control (RBAC): Restricting access to resources based on user roles and responsibilities helps minimize the potential for unauthorized access and reduces the risk of insider threats.
Monitoring and alerting: Implementing real-time monitoring and alerting systems enables organizations to detect and respond to security issues quickly, minimizing potential damage and downtime.
Establishing a Security-Centric Culture
Building a security-centric culture is crucial for ensuring a robust and secure CI/CD pipeline. Key elements of a security-centric culture include:
Collaboration between development, operations, and security teams: Encouraging collaboration and communication among these teams helps create a shared understanding of security goals and fosters a proactive approach to risk mitigation.
Comprehensive training programs for all team members: Providing security training to all members of the organization, regardless of their role, helps raise awareness about potential risks and fosters a shared responsibility for security.
Proactive risk mitigation, compliance, and customer trust: By adopting a security-first mindset, organizations can proactively address potential risks, ensure compliance with industry standards and regulations, and build trust with customers by demonstrating a commitment to data security and privacy.
Cloud Security Web’s Security-First Approach
Cloud Security Web focuses on providing solutions for API integration and cloud security, emphasizing the importance of a security-first approach in managing APIs and integrations. Key aspects of this approach include:
Expertise in API and integration governance: With a team of experienced professionals, Cloud Security Web offers in-depth knowledge and expertise in API and integration governance, helping organizations manage their APIs and integrations securely and efficiently.
Integration best practices library: Cloud Security Web provides access to a repository of pre-built integration code and best practices, enabling organizations to improve the performance, reliability, and security of their APIs and integrations.
Services offered, including security-first pipelines and API quality assurance: The company offers a range of services, such as staff augmentation, professional staffing, IT services, security and compliance, security-first pipelines, and API quality assurance, catering to the unique needs of organizations that use APIs and integrations in their business operations.
Secure Your Development Process
Implementing security-first pipelines for CI/CD can significantly benefit organizations by ensuring a more secure and reliable development process. By adopting best practices, automating security tasks, and establishing a security-centric culture, organizations can mitigate risks and maintain compliance. As a reliable and trusted partner in API and integration governance, Cloud Security Web offers a range of services, including staff augmentation, professional staffing, IT services, security-first pipelines, and API quality assurance. Explore Cloud Security Web’s services and solutions for API integration and cloud security to elevate your organization’s security posture. Discover more today.