Welcome to the comprehensive guide on securing your data. Data security is of utmost importance for individuals and organizations alike. From personal information to sensitive business data, the threat of cyberattacks looms large. This guide aims to provide you with essential insights, strategies, and best practices to safeguard your data effectively. We will explore the various aspects of data security, including encryption, access control, data backup, and security protocols. By understanding the risks and implementing robust security measures, you can protect your data from unauthorized access, breaches, and loss. Whether you are a cybersecurity enthusiast, a business owner, or simply someone concerned about protecting your information, this guide is designed to equip you with the knowledge and tools needed to enhance your data security posture. Join us on this journey to fortify your defenses and secure your valuable data assets.
Common Threats to Data Security
Overview of Cyber Threats Targeting Data
Cyber threats are constantly evolving, posing significant risks to data security. Understanding the common threats can help individuals and organizations better protect their sensitive information. Some of the prevalent cyber threats include:.
-
Phishing Attacks: Phishing is a common tactic used by cybercriminals to trick individuals into providing sensitive information such as login credentials or personal details. These attacks are often carried out through deceptive emails or messages.
-
Malware Infections: Malware, including viruses, worms, ransomware, and spyware, can infect systems and steal or damage data. Malicious software is often distributed through infected websites, email attachments, or removable devices.
-
Insider Threats: While external threats are a major concern, insider threats from employees or individuals with authorized access can also compromise data security. These threats may be intentional or unintentional.
-
DDoS Attacks: Distributed Denial of Service (DDoS) attacks flood a system with an overwhelming amount of traffic, causing it to become slow or unresponsive. This can disrupt services and lead to data breaches.
Examples of Data Security Vulnerabilities
Data security vulnerabilities can exist in various forms within an organization’s infrastructure or practices. Some examples include:.
-
Weak Passwords: Using weak or easily guessable passwords can make it easier for cybercriminals to gain unauthorized access to systems and sensitive data.
-
Unencrypted Data: Failure to encrypt sensitive data leaves it vulnerable to interception and exploitation. Encrypting data can help protect it from unauthorized access.
-
Lack of Regular Updates: Failing to apply security patches and updates to software and systems can leave them susceptible to known vulnerabilities that cyber attackers can exploit.
-
Social Engineering: Social engineering tactics involve manipulating individuals to divulge confidential information. Attackers use psychological manipulation to deceive individuals into disclosing sensitive data.
Emerging Threats in Data Security
In addition to the common threats mentioned above, the landscape of data security is constantly evolving, giving rise to new challenges. Some emerging threats include:.
-
AI-Powered Attacks: As artificial intelligence (AI) technology advances, cybercriminals are leveraging AI to conduct sophisticated attacks, such as generating convincing phishing emails or bypassing security measures.
-
IoT Vulnerabilities: The proliferation of Internet of Things (IoT) devices introduces new entry points for cyber attackers to exploit. Weak security measures in IoT devices can lead to data breaches and network intrusions.
-
Supply Chain Attacks: Targeting the supply chain has become a lucrative tactic for cybercriminals. By compromising a trusted vendor or partner, attackers can infiltrate systems and exfiltrate sensitive data.
Protecting Against Data Security Threats
To enhance data security and mitigate risks, individuals and organizations can implement the following measures:.
-
Regular Security Audits: Conducting frequent security audits can help identify vulnerabilities and gaps in existing security protocols.
-
Data Encryption: Utilize strong encryption methods to protect sensitive data both at rest and in transit.
-
Employee Training: Educate employees on best practices for data security, including how to recognize and respond to potential threats.
-
Incident Response Planning: Develop and regularly review incident response plans to effectively respond to security incidents and minimize their impact.
By staying informed about emerging threats, adopting proactive security measures, and fostering a culture of cybersecurity awareness, individuals and organizations can strengthen their defenses against data security threats and safeguard their valuable information.
Best Practices for Securing Data
Where data is a valuable asset, securing sensitive information is paramount for any organization. Implementing robust security measures not only protects data from unauthorized access but also instills trust among customers and stakeholders. Let’s delve deeper into the best practices for securing data:.
Implementing Encryption as a Protective Measure
Encryption plays a vital role in safeguarding data. By converting plaintext information into ciphertext using complex algorithms, encryption ensures that even if unauthorized individuals intercept the data, they cannot decipher it without the encryption key. Organizations should implement end-to-end encryption to protect data both in transit and at rest.
Enforcing Strong Access Controls
Another critical aspect of data security is enforcing stringent access controls. This involves implementing measures such as multi-factor authentication, least privilege access, role-based access control, and regular access reviews. By limiting access to sensitive data to only authorized personnel, organizations can reduce the risk of data breaches due to insider threats or compromised credentials.
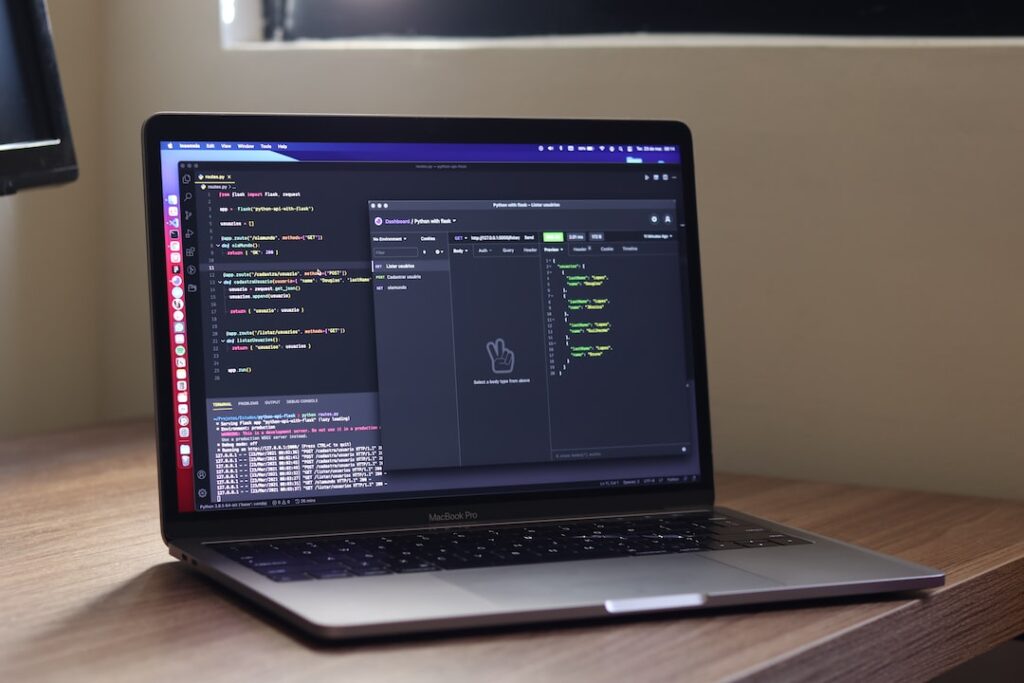
Regularly Updating Security Software
To stay ahead of evolving cyber threats, it is crucial to regularly update security software. This includes installing patches, updates, and security fixes for operating systems, applications, antivirus software, firewalls, and intrusion detection systems. Outdated software may contain known vulnerabilities that cybercriminals can exploit to gain unauthorized access to data.
Conducting Security Audits
Conducting periodic security audits is essential for evaluating the effectiveness of existing security controls and identifying potential vulnerabilities. By conducting penetration testing, vulnerability assessments, and security compliance audits, organizations can proactively address security gaps and enhance their overall security posture.
Implementing Data Loss Prevention Measures
Data loss prevention (DLP) solutions can help organizations monitor, detect, and prevent the unauthorized exfiltration of sensitive data. By implementing DLP policies, organizations can enforce data protection rules, monitor data movement, and prevent data leakage through various channels such as email, removable storage devices, and cloud applications.
Educating Employees on Security Best Practices
Human error remains one of the leading causes of data breaches. Organizations should invest in cybersecurity awareness training programs to educate employees about the importance of data security, phishing awareness, password hygiene, and social engineering tactics. By fostering a culture of security awareness, organizations can empower employees to be vigilant against cyber threats.
By adhering to these best practices for securing data, organizations can fortify their defenses against cyber threats, enhance data privacy, and maintain the trust of their customers and stakeholders. Prioritizing data security is not just a compliance requirement but a strategic imperative in today’s digital landscape.
Data Protection Regulations
Overview of GDPR and its Impact on Data Protection
The General Data Protection Regulation (GDPR) is a comprehensive data protection law that came into effect in the European Union in 2018. It has significantly impacted how organizations handle personal data, emphasizing transparency, accountability, and user consent. Understanding the key principles of GDPR, such as data minimization, purpose limitation, and data subject rights, is crucial for businesses to ensure compliance and protect individuals’ privacy.
Other Important Data Protection Laws and Compliance Standards
Apart from GDPR, various other data protection laws and compliance standards exist globally to safeguard personal information. For example, the California Consumer Privacy Act (CCPA) in the United States grants consumers certain rights regarding their data. Additionally, industry-specific regulations like the Health Insurance Portability and Accountability Act (HIPAA) for healthcare data and the Payment Card Industry Data Security Standard (PCI DSS) for payment card information establish specific requirements for data protection in those sectors.
Staying abreast of these regulations and standards is essential for organizations to avoid legal repercussions, maintain customer trust, and uphold data security best practices.
Importance of Compliance with Data Protection Regulations
Compliance with data protection regulations is not just a legal requirement but also a strategic business imperative. Non-compliance can result in hefty fines, damaged reputation, and loss of customer trust. By adhering to these regulations, organizations demonstrate their commitment to respecting individual privacy rights and fostering a secure digital environment.
Data Protection Measures for Enhanced Security
In addition to complying with regulations, implementing robust data protection measures is crucial to safeguard sensitive information. Encryption, access controls, regular audits, and employee training on data handling practices are essential components of a comprehensive data protection strategy. By adopting a proactive approach to security, organizations can mitigate risks associated with data breaches and cyber threats.
The Role of Data Protection Officers
Many regulations, including GDPR, require the appointment of a Data Protection Officer (DPO) to oversee data protection activities within an organization. DPOs play a vital role in ensuring compliance, conducting risk assessments, and serving as a point of contact for data protection authorities and individuals. Their expertise helps organizations navigate complex regulatory landscapes and implement effective data protection practices.
Emerging Trends in Data Protection
With advancements in technology and evolving cyber threats, the field of data protection continues to evolve. Concepts such as Privacy by Design, which advocates for privacy considerations from the outset of system design, and the increasing focus on cross-border data transfers present new challenges and opportunities for organizations. Staying informed about these trends is essential for adapting data protection strategies to meet changing regulatory requirements and cybersecurity needs.
Data protection regulations form the cornerstone of privacy and security in the digital age. By understanding the nuances of these laws, implementing robust security measures, and staying proactive in compliance efforts, organizations can not only protect sensitive data but also build trust with their customers and stakeholders.
Securing Data in Businesses
Data security is a critical aspect for businesses of all sizes. From customer information to proprietary data, organizations must implement robust strategies to safeguard their sensitive data. This blog section will delve into the realm of securing data in businesses, shedding light on the following key areas: Enterprise-level Data Protection Strategies and Employee Training on Data Security.
Fortifying Enterprise-level Data Protection
- The Role of Data Classification
- Network Segmentation for Enhanced Security
- Intrusion Detection and Prevention Systems
- Data Encryption Best Practices
- Cloud Security Considerations
In the dynamic landscape of data security, organizations must begin by classifying their data based on sensitivity levels to apply appropriate security controls effectively. Network segmentation helps in containing breaches and limiting lateral movement within a network, thereby bolstering overall security posture. Implementing robust Intrusion Detection and Prevention Systems can proactively identify and thwart potential threats, ensuring data integrity. Furthermore, following data encryption best practices is paramount to safeguarding information from unauthorized access. With the proliferation of cloud services, businesses must also prioritize cloud security measures to protect data stored and processed in cloud environments.
Empowering Employees through Comprehensive Training
- Role-based Security Training Programs
- Simulated Phishing Exercises
- Incident Response Simulations
- Mobile Device Security Guidelines
- Regulatory Compliance Training
Empowering employees with the knowledge and skills to recognize and respond to security threats is instrumental in fortifying the human element of data security. Role-based security training programs tailored to different job functions can enhance awareness and adherence to security protocols. Conducting simulated phishing exercises can help assess employees’ susceptibility to phishing attacks and reinforce best practices. Regular incident response simulations enable staff to practice coordinated responses to security incidents, minimizing potential damages. Establishing clear guidelines for mobile device security and providing regulatory compliance training ensure that employees understand their responsibilities in maintaining data security standards.
By focusing on these pivotal aspects of data security, businesses can establish a robust defense mechanism against cyber threats, safeguarding their assets and maintaining trust with stakeholders. Continuous monitoring, regular updates, and proactive measures are essential to adapt to the evolving threat landscape and uphold data confidentiality and integrity.
Protecting Personal Data
Protecting personal data has become more crucial than ever. With cyber threats on the rise, individuals need to take proactive steps to secure their sensitive information both on personal devices and online. Let’s delve into some key points to consider:.
-
Securing Sensitive Information on Personal Devices.
- Implement strong passwords and biometric authentication on your devices.
- Enable encryption for data stored on your devices to prevent unauthorized access.
- Keep your operating system and applications up to date to patch any security vulnerabilities.
- Be cautious when connecting to public Wi-Fi networks to avoid potential data breaches.
- Regularly back up your data to a secure location to prevent data loss in case of a security incident.
-
Tips for Safeguarding Personal Data Online.
- Use unique and complex passwords for each online account to minimize the risk of multiple accounts being compromised.
- Enable two-factor authentication whenever possible to add an extra layer of security to your accounts.
- Be wary of phishing attempts and avoid clicking on suspicious links or providing personal information to unknown sources.
- Review privacy settings on social media platforms and limit the amount of personal information shared publicly.
- Consider using a reputable virtual private network (VPN) when browsing the internet to protect your data from prying eyes.
In addition to the above points, it is essential to understand the importance of data privacy laws and regulations that govern the protection of personal data. Familiarize yourself with laws such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) to know your rights and responsibilities regarding personal data.
Furthermore, staying informed about the latest cybersecurity threats and trends can help individuals stay one step ahead of potential risks. Subscribing to cybersecurity blogs, attending webinars, and following reputable cybersecurity experts on social media can provide valuable insights into emerging threats and best practices for data protection.
Continuous education and awareness are key components of maintaining personal data security. Consider taking online courses or workshops on cybersecurity topics to enhance your knowledge and skills in safeguarding sensitive information.
By adopting a proactive approach to personal data protection, individuals can mitigate the risks associated with cyber threats and safeguard their privacy in an increasingly digital world.
Emerging Technologies in Data Security
Role of AI and Machine Learning in Data Protection
- The Evolving Role of AI and Machine Learning in Enhancing Data Security
- Exploring Examples of AI and Machine Learning Applications in Data Protection
- Unveiling the Benefits of Utilizing AI and Machine Learning in Safeguarding Data
- Understanding the Potential of AI and Machine Learning in Future Data Security Trends
Blockchain Technology for Secure Data Transactions
- Demystifying Blockchain Technology and Its Vital Role in Data Security
- Ensuring Secure Data Transactions through Blockchain’s Immutable Ledger
- Real-world Applications Showcasing the Efficacy of Blockchain in Data Protection
- Harnessing the Advantages of Blockchain for Establishing Trust in Data Transactions
The importance of robust data security measures cannot be overstated. As organizations grapple with the increasing volume and complexity of data, leveraging emerging technologies has become imperative to ensure the confidentiality, integrity, and availability of sensitive information.
One of the groundbreaking developments in data security is the integration of AI and machine learning algorithms. These technologies have revolutionized the traditional approach to safeguarding data by enabling proactive threat detection, anomaly identification, and adaptive security mechanisms. By continuously learning from vast datasets, AI and machine learning systems can detect and mitigate potential security breaches in real-time, offering a proactive defense against evolving cyber threats.
Furthermore, blockchain technology has emerged as a game-changer in ensuring secure data transactions. By employing cryptographic principles and decentralized consensus mechanisms, blockchain creates an immutable ledger that enhances data integrity and transparency. Transactions recorded on a blockchain are tamper-proof, providing a secure and verifiable record of events. This decentralized approach not only minimizes the risk of data manipulation but also reduces the reliance on centralized authorities, fostering trust among transaction participants.
Real-world applications across industries, from finance to supply chain management, demonstrate the transformative impact of blockchain in enhancing data security. Whether preventing fraudulent activities or enabling traceability in complex networks, blockchain offers a decentralized solution to data protection challenges.
The convergence of AI, machine learning, and blockchain technologies represents a pivotal moment in the realm of data security. By embracing these innovative solutions, organizations can fortify their defenses, mitigate risks, and adapt to the dynamic cybersecurity landscape. As the digital ecosystem continues to evolve, staying abreast of emerging technologies will be key to ensuring resilient data protection strategies.
Data Breach Response Plan
Creating a Data Breach Response Plan
Data breaches have become a common occurrence. Companies of all sizes are vulnerable to cyber attacks, making it crucial to have a well-defined data breach response plan in place. Here are the key steps to creating an effective response plan:.
-
Risk Assessment : Identify potential risks and vulnerabilities in your systems that could lead to a data breach.
-
Response Team Formation : Create a dedicated team responsible for managing and responding to data breaches. This team should include IT professionals, legal experts, communication specialists, and senior management.
-
Incident Detection and Reporting : Implement tools and processes to detect and report any data breaches in a timely manner. This could include intrusion detection systems, security information and event management (SIEM) tools, and employee training on recognizing potential security incidents.
-
Containment and Eradication : Act swiftly to contain the breach and prevent further unauthorized access to sensitive data. This may involve isolating affected systems, shutting down compromised accounts, and removing malware.
-
Communication Plan : Develop a clear communication plan for internal and external stakeholders. Transparency is key in maintaining trust, so be prepared to communicate openly about the breach, its impact, and the steps being taken to address it.
-
Legal and Regulatory Compliance : Ensure that your response plan complies with relevant data protection laws and regulations. This may involve reporting the breach to authorities, notifying affected individuals, and offering support services as required.
Steps to Mitigate Data Breach Impacts
Despite best efforts to prevent data breaches, they can still occur. In addition to having a response plan in place, here are some key steps to mitigate the impacts of a data breach:.
-
Data Encryption : Encrypt sensitive data to make it unreadable in the event of a breach. This can help prevent unauthorized access to confidential information.
-
Regular Security Audits : Conduct regular security audits and penetration testing to identify and address vulnerabilities in your systems before they can be exploited by cybercriminals.
-
Employee Training : Provide comprehensive training to employees on data security best practices. Human error is a common cause of data breaches, so educating staff on how to handle sensitive information can help reduce risks.
-
Data Backup and Recovery : Regularly back up your data and test your backup systems to ensure that you can quickly recover in the event of a breach or system failure.
-
Monitoring and Incident Response Testing : Monitor your systems for unusual activity and conduct regular incident response drills to test the effectiveness of your response plan.
By following these steps and being prepared with a well-thought-out response plan, businesses can better protect themselves from the damaging effects of data breaches.
Conclusion
Safeguarding your data is crucial in today’s digital age. By following the comprehensive guide outlined in this blog, you can take proactive steps to protect your sensitive information from cyber threats. Remember, data security is not a one-time task but an ongoing process that requires diligence and attention to detail. Stay informed, implement best practices, and be vigilant in order to keep your data safe and secure.