Securing Hybrid Cloud Environments

As organizations increasingly integrate on-premises and cloud resources, the demand for robust security in hybrid cloud environments escalates. To ensure data protection and compliance, a comprehensive security strategy is indispensable. By adhering to a set of well-defined security guidelines and best practices, organizations can navigate the complexities of hybrid cloud setups effectively. This guide delves into key considerations aimed at fortifying the security posture, minimizing risks, and establishing a secure foundation for hybrid cloud operations. Embracing these insights will empower organizations to safeguard their data and applications in the hybrid cloud landscape.
Best Practices for Hybrid Cloud Security
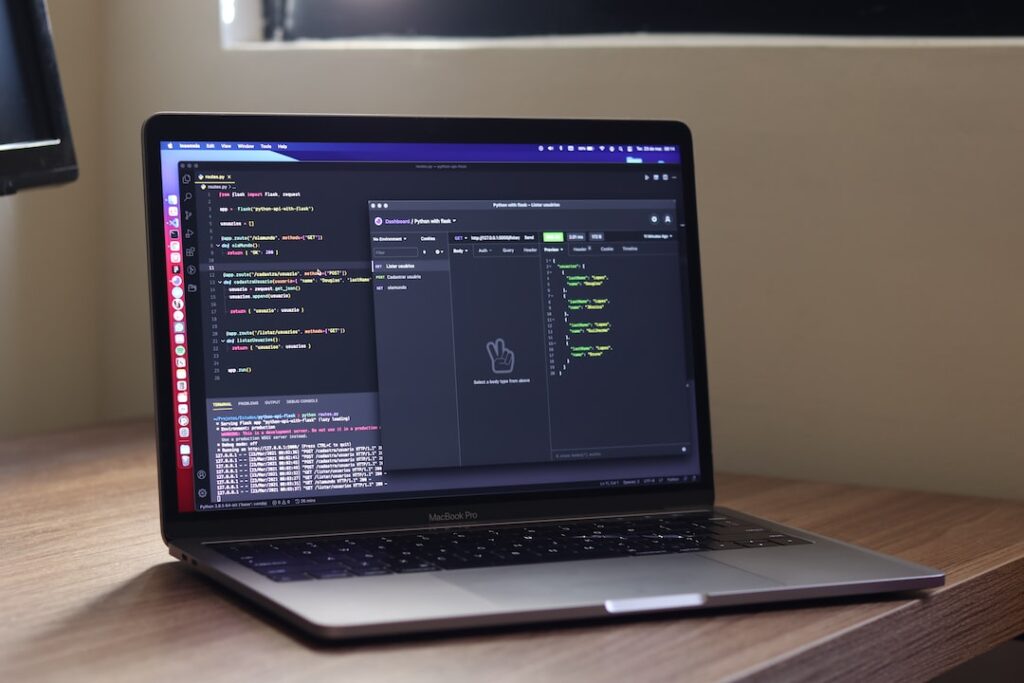
Implementing Multi-Factor Authentication (MFA)
In the realm of hybrid cloud security, implementing Multi-Factor Authentication (MFA) is a crucial step towards safeguarding your data and resources. MFA adds an extra layer of security by requiring users to provide multiple forms of verification before granting access. This can include something they know (like a password), something they have (like a code sent to their phone), or something they are (like a fingerprint). By incorporating MFA into your hybrid cloud environment, you significantly reduce the risk of unauthorized access and data breaches.
Regularly Updating and Patching Systems
Another essential best practice for hybrid cloud security is to regularly update and patch your systems. Software updates often contain security patches that address vulnerabilities and strengthen defenses against cyber threats. Failure to keep your systems up to date exposes them to known vulnerabilities that malicious actors can exploit. By staying current with updates and patches, you ensure that your hybrid cloud environment is equipped with the latest security measures to mitigate risks.
Securing Data with Encryption
Securing data with encryption is paramount for protecting sensitive information in a hybrid cloud setup. Encryption converts data into a coded format that can only be deciphered with the appropriate decryption key, making it unreadable to unauthorized parties. Whether data is at rest, in transit, or in use, employing robust encryption mechanisms adds a layer of defense against data breaches and unauthorized access. By encrypting your data, you enhance confidentiality and data integrity, bolstering the overall security posture of your hybrid cloud infrastructure.
Implementing Network Segmentation
Network segmentation involves dividing a computer network into subnetworks to enhance security and control access. By segmenting your hybrid cloud network, you can isolate critical assets, applications, or services, limiting the potential impact of a security breach. This practice helps contain threats within specific segments, preventing lateral movement by cyber attackers. Implementing network segmentation alongside other security measures fortifies your hybrid cloud environment against sophisticated attacks.
Conducting Regular Security Audits
Conducting regular security audits is essential for evaluating the effectiveness of your hybrid cloud security measures. Audits provide insights into potential vulnerabilities, compliance gaps, or outdated security protocols that need attention. By performing comprehensive security audits at scheduled intervals, you can identify and address security weaknesses proactively, ensuring that your hybrid cloud infrastructure remains resilient against evolving cyber threats.
Establishing Incident Response Protocols
Establishing incident response protocols is critical for effectively managing security incidents and minimizing their impact. In the event of a security breach or data compromise in your hybrid cloud environment, having well-defined incident response procedures helps your organization respond promptly and decisively. These protocols outline the steps to contain the incident, investigate the root cause, mitigate damages, and restore normal operations. By establishing clear incident response protocols and conducting regular drills, you can enhance your organization’s readiness to handle security incidents with efficiency and effectiveness.
Enhancing Security Measures
Where cyber threats are constantly evolving, it is crucial for individuals and organizations to prioritize security measures to safeguard their data and systems. This blog section will delve into two important strategies for enhancing security measures.
Monitoring Network Traffic and Activities
One key aspect of enhancing security measures is monitoring network traffic and activities. By monitoring network traffic, organizations can detect any unusual patterns or suspicious activities that could indicate a potential security breach. Implementing network monitoring tools and intrusion detection systems can provide real-time alerts and insights into network behavior, allowing for immediate action to mitigate any threats. Additionally, setting up firewalls and implementing strong access control mechanisms can further enhance network security.
Conducting Regular Security Audits and Assessments
Another critical strategy for enhancing security measures is conducting regular security audits and assessments. Security audits involve a comprehensive review of an organization’s security policies, procedures, and controls to identify any weaknesses or vulnerabilities. By performing regular security assessments, organizations can proactively address any security gaps and ensure that their security measures are up to date and effective. Furthermore, penetration testing can be utilized to simulate real-world cyber attacks and identify potential entry points for hackers, enabling organizations to strengthen their defenses.
Incorporating Employee Training
Apart from technical measures, educating employees on cybersecurity best practices is essential for enhancing overall security. Conducting regular training sessions to raise awareness about common cyber threats, phishing scams, and social engineering tactics can empower employees to recognize and respond to potential security risks effectively. Additionally, enforcing strong password policies and promoting a culture of security consciousness within the organization can greatly contribute to bolstering defenses against cyber threats.
Utilizing Multi-Factor Authentication
Implementing multi-factor authentication (MFA) is another key practice to enhance security measures. MFA adds an extra layer of protection by requiring users to provide multiple forms of verification before gaining access to systems or data. This significantly reduces the risk of unauthorized access, even if login credentials are compromised, as the additional authentication factor acts as a barrier against potential threats.
Continuous Security Updates and Patch Management
Regularly updating software, systems, and security patches is essential to mitigate vulnerabilities and protect against known exploits. Cyber attackers often target outdated software with known security flaws, making timely updates crucial for maintaining a secure environment. Automated patch management tools can streamline the process of deploying updates across all devices and systems, ensuring that security vulnerabilities are promptly addressed.
Conclusion
By implementing a multi-faceted approach that combines technical solutions, regular assessments, employee training, MFA implementation, and proactive patch management, individuals and organizations can significantly enhance their security measures and reduce the likelihood of falling victim to cyber attacks. Prioritizing security not only protects sensitive data but also preserves trust and credibility in an increasingly interconnected digital landscape.
Establishing Robust Security Policies
Where cyber threats are constantly evolving, establishing robust security policies is paramount for organizations to safeguard their sensitive information and assets. Security policies serve as the foundation for a secure environment by providing clear guidelines on data protection, access controls, incident response, and compliance standards.
Developing Clear Security Policies and Procedures
Developing comprehensive security policies and procedures involves a systematic approach to addressing potential security risks and vulnerabilities. Organizations need to conduct thorough risk assessments to identify potential threats and determine the appropriate countermeasures. By outlining specific policies for data encryption, user authentication, network security, and physical security measures, businesses can create a structured framework for maintaining a secure environment.
Educating Employees on Security Best Practices
While technology plays a crucial role in cybersecurity, human error remains a significant factor in security breaches. Therefore, educating employees on security best practices is essential in fortifying the overall security posture. Organizations should prioritize ongoing training programs that cover topics such as password management, social engineering awareness, and incident response protocols. By empowering staff with the knowledge and skills to identify and respond to security risks, organizations can reduce the likelihood of successful cyber attacks.
Implementing Security Awareness Programs
In addition to formal training sessions, implementing security awareness programs can further enhance employees’ understanding of cybersecurity best practices. These programs can include interactive workshops, phishing simulations, and cybersecurity awareness campaigns to reinforce the importance of vigilance and adherence to security protocols. By fostering a culture of security awareness within the organization, employees become active participants in maintaining a secure work environment.
Monitoring and Continuous Improvement
Establishing robust security policies is an ongoing process that requires regular monitoring and continuous improvement. Organizations should implement mechanisms for monitoring security metrics, conducting periodic security audits, and assessing the effectiveness of existing security controls. By staying vigilant and responsive to emerging threats, organizations can adapt their security policies to mitigate risks and enhance their overall security posture.
Establishing robust security policies and educating employees on security best practices are essential components of a comprehensive cybersecurity strategy. By prioritizing security at all levels of the organization and fostering a culture of awareness and vigilance, businesses can effectively protect their valuable assets and sensitive information from evolving cyber threats.
Ensuring Resilience and Recovery
The importance of ensuring resilience and recovery within organizations cannot be overstated. This blog section will delve into two critical aspects vital for maintaining business continuity: creating backup and disaster recovery plans, and implementing access controls and segregation.
Creating Comprehensive Backup and Disaster Recovery Plans
A cornerstone of resilience is having a comprehensive backup and disaster recovery plan in place. This involves not just backing up critical data and systems but also creating a detailed strategy that outlines the procedures to be followed in case of a data loss incident or a disaster. Organizations should consider factors such as data encryption, secure storage locations, and the use of advanced technologies like continuous data protection to minimize recovery time and data loss. Regularly testing the recovery process through simulated drills can help identify gaps and improve the overall efficacy of the plan.
Moreover, the rise of ransomware attacks and other sophisticated cyber threats underscores the need for a multi-layered approach to data protection. Implementing immutable backups, which are copies of data that cannot be altered or deleted, can provide an added layer of defense against ransomware attacks, ensuring that organizations can recover their data even if primary systems are compromised.
Enhancing Access Controls and Segregation Measures
Access controls form the frontline defense against unauthorized access and data breaches. Organizations should adopt a Zero Trust security model, where access is granted on a least-privileged basis and continuously verified. Role-based access control (RBAC), attribute-based access control (ABAC), and continuous authentication mechanisms can help bolster the security posture of an organization.
In addition to access controls, segregation of duties remains a critical practice in ensuring accountability and preventing fraud. By dividing responsibilities among different individuals, organizations can establish checks and balances that reduce the risk of malicious activities going undetected. Regularly auditing access logs and conducting security assessments can help identify anomalies and proactively address potential security vulnerabilities.
By creating robust backup and disaster recovery plans, and implementing stringent access controls and segregation measures, organizations can fortify their resilience against a myriad of threats. Embracing a proactive stance towards cybersecurity, coupled with continuous training and awareness programs, will empower organizations to navigate the evolving threat landscape and emerge stronger from any potential disruptions.
Conclusion
Implementing the 10 tips for hybrid cloud security can significantly enhance the overall security posture of an organization’s cloud environment. By combining best practices for both public and private cloud security, businesses can effectively mitigate risks, protect sensitive data, and ensure compliance with regulatory requirements. Embracing a proactive approach to security and staying vigilant against emerging threats are key elements in safeguarding the integrity and confidentiality of cloud-based assets in a hybrid environment.