Introduction

Efficient data synchronization is a cornerstone of robust cloud security measures. As organizations increasingly rely on cloud services for data storage and management, the need to ensure accurate and timely synchronization across platforms becomes vital. Enhancing data synchronization processes is crucial for safeguarding sensitive information and fortifying security protocols. By addressing challenges and implementing effective strategies, businesses can bolster their defenses against potential threats and prevent data breaches. This introduction delves into the complex realm of data synchronization in cloud environments, highlighting the significance of streamlined processes and the benefits they offer to modern cybersecurity practices.
Challenges in Data Synchronization for Cloud Security
Bandwidth Limitations
- One of the primary challenges in data synchronization for cloud security is bandwidth limitations. Transferring large volumes of data to and from the cloud can be hindered by bandwidth constraints, leading to slow synchronization processes and potential bottlenecks. Organizations need to implement efficient data transfer protocols and optimize bandwidth usage to overcome this challenge.
Data Consistency
- Maintaining data consistency across multiple cloud environments and on-premises systems is another critical challenge in cloud security. Inconsistent data synchronization can result in data corruption, compliance issues, and security vulnerabilities. Implementing data consistency checks, version control mechanisms, and synchronization validation processes is essential for ensuring data integrity and security in the cloud.
Security Concerns
- Security is a paramount concern in cloud data synchronization. The transfer of sensitive data between on-premises infrastructure and cloud environments introduces security risks such as data breaches, unauthorized access, and data manipulation. Encryption, access control mechanisms, data masking, and secure authentication protocols are vital components of a robust cloud security strategy to mitigate security concerns in data synchronization.
Bandwidth Limitations: Strategies to Enhance Data Transfer Efficiency
- To combat bandwidth limitations, organizations can leverage data compression techniques, prioritize data transfers based on criticality, and implement caching mechanisms to reduce the volume of data transmitted. By adopting a data-centric approach and utilizing bandwidth optimization tools, businesses can streamline synchronization processes and accelerate data transfer speeds.
Data Consistency: Best Practices for Seamless Synchronization
- Achieving data consistency in a multi-cloud environment requires adherence to best practices such as establishing a single source of truth, implementing data validation mechanisms, and conducting regular audits to detect inconsistencies. By fostering a culture of data integrity and deploying automated synchronization tools, organizations can maintain consistent data across disparate cloud platforms.
Security Concerns: Strengthening Cloud Security Posture
- Enhancing cloud security involves deploying robust encryption algorithms, enforcing strict access controls, and conducting regular security assessments to identify vulnerabilities. By integrating threat intelligence feeds, implementing real-time monitoring solutions, and fostering a security-first mindset, businesses can fortify their cloud infrastructure and protect sensitive data from potential cyber threats.
The evolving landscape of cloud computing underscores the importance of addressing challenges in data synchronization to fortify cloud security defenses. By proactively mitigating bandwidth limitations, ensuring data consistency, and fortifying security measures, organizations can establish a resilient security posture that safeguards critical data assets in the cloud.
Strategies to Enhance Data Synchronization in Cloud Security
In the realm of cloud security, ensuring that data synchronization is efficient and secure is paramount. Here are key strategies to enhance data synchronization in cloud security:.
- Utilizing Encryption Techniques for Enhanced Security
Data encryption plays a critical role in safeguarding sensitive information in cloud environments. Employing advanced encryption standards like AES (Advanced Encryption Standard) ensures that data remains protected both at rest and in transit. Encryption not only secures data during synchronization but also provides an additional layer of defense against unauthorized access.
- Implementing Real-Time Data Monitoring Solutions
Real-time data monitoring is essential for proactive threat detection and incident response. By implementing robust monitoring tools such as intrusion detection systems (IDS) and security information and event management (SIEM) platforms, organizations can continuously monitor data synchronization activities for any suspicious behavior. This real-time visibility enables swift identification of security incidents, allowing for immediate remediation to prevent data breaches.
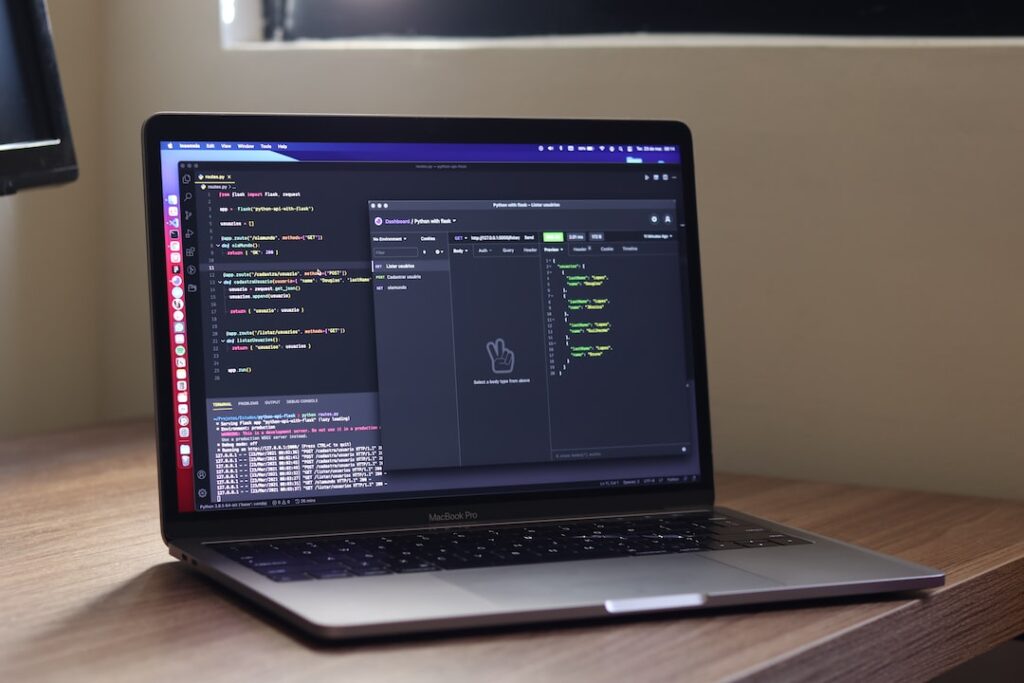
- Leveraging Automation for Efficient Synchronization Processes
Automation streamlines data synchronization tasks, improving efficiency and accuracy. Automated processes help in reducing manual errors and ensuring consistency across cloud environments. By utilizing automation tools and scripts, organizations can schedule synchronization tasks, monitor progress, and quickly address any synchronization failures. Automated synchronization not only enhances operational efficiency but also minimizes the risk of data inconsistencies.
- Enhancing Data Integrity with Checksum Verification
In addition to encryption and monitoring, implementing checksum verification mechanisms can further enhance data integrity during synchronization. Checksums serve as unique identifiers for data blocks, allowing systems to verify the integrity of transmitted data. By verifying checksums before and after synchronization, organizations can detect any data corruption or tampering, ensuring the reliability of synchronized data.
- Continuous Security Auditing and Compliance Checks
Regular security audits and compliance checks are vital to maintaining a strong security posture in cloud environments. Conducting periodic audits helps in identifying vulnerabilities, ensuring adherence to security best practices, and validating compliance with industry regulations. By consistently evaluating security controls and configurations, organizations can mitigate risks and enhance the overall security of data synchronization processes.
By incorporating these strategies – utilizing encryption techniques, implementing real-time data monitoring, leveraging automation for synchronization, enhancing data integrity with checksum verification, and conducting regular security audits – organizations can strengthen their data synchronization practices in cloud security. These proactive measures not only enhance security defenses but also foster a culture of continuous improvement and vigilance in safeguarding sensitive data.
Tools and Technologies for Efficient Data Synchronization
Cloud-Based Data Sync Solutions
Data synchronization plays a vital role in ensuring seamless communication and collaboration across various platforms and devices. Cloud-based data sync solutions have emerged as a game-changer in this realm, offering organizations the ability to synchronize data in real-time across multiple locations. By leveraging cloud infrastructure, businesses can achieve high availability, scalability, and reliability in data synchronization processes. These solutions often utilize advanced algorithms to detect changes in data and efficiently propagate these changes to all connected devices, ensuring data consistency and integrity. Moreover, cloud-based data sync solutions provide a cost-effective way for businesses to manage their data synchronization needs without the burden of maintaining complex infrastructure.
Blockchain for Secure Data Synchronization
As data security continues to be a top priority for businesses, blockchain technology has gained traction as a secure data synchronization tool. The decentralized and immutable nature of blockchain ensures that data synchronization is tamper-proof and transparent. Blockchain’s consensus mechanisms and cryptographic features make it highly resilient to unauthorized tampering, making it an ideal solution for secure data synchronization across distributed networks. Additionally, blockchain enables secure data sharing among multiple parties without the need for a trusted intermediary, enhancing data privacy and security.
Hybrid Approaches for Data Synchronization
In addition to cloud-based solutions and blockchain technology, hybrid approaches combining the strengths of both paradigms are increasingly being adopted for data synchronization. These hybrid models leverage the scalability and efficiency of cloud-based solutions while harnessing the security and trust features of blockchain technology. By integrating cloud services with blockchain frameworks, organizations can create a robust data synchronization ecosystem that offers the best of both worlds. This hybrid approach not only ensures data integrity and security but also enhances the scalability and performance of data synchronization processes.
The adoption of cloud-based data sync solutions, blockchain technology, and hybrid approaches represents a significant advancement in achieving efficient and secure data synchronization practices. By leveraging the capabilities of these tools and technologies, organizations can streamline data management, enhance collaboration, and bolster data security in an increasingly interconnected digital landscape.
Future Trends in Data Synchronization and Cloud Security
AI-Driven Synchronization Algorithms: Enhancing Efficiency and Accuracy
In the realm of data synchronization and cloud security, the integration of artificial intelligence (AI) has paved the way for significant advancements. AI-driven synchronization algorithms have emerged as a powerful tool, revolutionizing how data is managed and synchronized across diverse platforms. These sophisticated algorithms possess the ability to analyze and adapt to data patterns, resulting in more efficient and accurate synchronization processes. By leveraging machine learning and predictive analytics, AI-driven algorithms can preemptively identify potential synchronization issues, thereby streamlining data exchange and ensuring data integrity.
Edge Computing Impact: Revolutionizing Data Processing and Security
Parallel to the advancements in AI-driven synchronization, the rise of edge computing is reshaping the landscape of data synchronization and cloud security. With the proliferation of Internet of Things (IoT) devices and the escalating demand for real-time data processing, edge computing has emerged as a pivotal technology. By decentralizing computation and data storage, edge computing brings processing capabilities closer to the data source, thereby reducing latency and enhancing synchronization efficiency. This proximity to data generation points not only accelerates data processing but also fortifies data security by minimizing data exposure during transit.
Future Prospects and Industry Implications
Looking ahead, the convergence of AI-driven synchronization algorithms and edge computing is poised to redefine the future of data synchronization and cloud security. The fusion of AI’s cognitive capabilities with edge computing’s decentralized approach promises to deliver unparalleled synchronization speed, accuracy, and security. Organizations that harness these technologies will gain a competitive edge in data-intensive environments, enabling them to optimize operations, enhance decision-making processes, and fortify data protection strategies.
As businesses navigate the complexities of data synchronization and cloud security, staying informed about these evolving trends is essential for maintaining resilience in an increasingly interconnected digital ecosystem. By embracing AI-driven synchronization algorithms and leveraging edge computing solutions, organizations can proactively adapt to the dynamic data landscape, positioning themselves for sustained success in the data-driven era.
Challenges and Opportunities in Implementation
While the potential benefits of AI-driven synchronization and edge computing are immense, their implementation poses certain challenges. Organizations must address issues such as data privacy concerns, compatibility with existing infrastructure, and the need for skilled professionals proficient in AI and edge computing technologies. Overcoming these challenges presents opportunities for innovation and growth, as companies that successfully integrate AI-driven synchronization and edge computing into their operations stand to gain improved efficiency, enhanced security, and a competitive edge in the market.
Regulatory Landscape and Ethical Considerations
The adoption of AI-driven synchronization algorithms and edge computing also raises important regulatory and ethical considerations. Data privacy regulations, such as the GDPR in Europe and the CCPA in California, impose strict requirements on the collection, storage, and processing of personal data. Organizations leveraging AI and edge computing technologies must ensure compliance with these regulations to avoid potential legal ramifications. Moreover, ethical considerations surrounding data usage, algorithm bias, and transparency in decision-making processes must be carefully navigated to uphold trust and integrity in data synchronization practices.
Conclusion
The future of data synchronization and cloud security is intricately tied to the advancements in AI-driven synchronization algorithms and the transformative impact of edge computing. By embracing these technologies, organizations can unlock new levels of efficiency, accuracy, and security in data synchronization processes. However, successful implementation requires a holistic approach that considers technical challenges, regulatory requirements, and ethical implications. As the digital landscape continues to evolve, staying abreast of future trends and adopting innovative solutions will be paramount for organizations seeking to thrive in a data-driven world.
Conclusion
Boosting data synchronization is crucial for enhancing cloud security measures. By ensuring that data is updated and consistent across multiple cloud environments in real-time, organizations can better protect their sensitive information and prevent security breaches. Implementing robust data synchronization practices will ultimately strengthen the overall security posture of cloud-based systems and help mitigate potential risks.