Importance of Distributed Models in Cloud Security

The importance of robust security measures is more pronounced than ever. As organizations increasingly adopt cloud technology, safeguarding sensitive information from cyber threats is a top priority. Utilizing distributed models in cloud security presents a forward-thinking approach to enhance protection and resilience. By spreading computing resources across various servers and locations, businesses can minimize the risk of a single point of failure and boost overall system performance. This strategy not only reinforces security protocols but also streamlines resource allocation, allowing seamless operational scalability. Amidst the ongoing cybersecurity challenges, integrating distributed models in cloud security serves as a proactive measure to strengthen defenses and mitigate potential risks. This innovative approach enables organizations to strike a balance between security, efficiency, and scalability, fostering a secure environment for digital innovation and advancement.
Benefits of Distributed Models
Scalability Enhancement in Cloud Security
Distributed models play a crucial role in enhancing scalability in cloud security. By distributing resources across multiple nodes or servers, the system can efficiently handle a growing amount of data and traffic without compromising performance. This scalability feature ensures that as the demand for services increases, the system can easily scale up to meet requirements, making it a cost-effective solution for businesses.
Enhanced Fault Tolerance
One of the significant advantages of distributed models is their ability to provide enhanced fault tolerance. In a distributed system, resources and workload are spread across multiple nodes. This redundancy ensures that if one node fails, the system can automatically reroute tasks to other functioning nodes, thereby preventing any service disruptions. This fault tolerance mechanism is critical for ensuring continuous service availability, especially in mission-critical applications.
Efficient Resource Utilization
Efficient resource utilization is another key benefit offered by distributed models. By distributing the workload evenly across multiple nodes, these models prevent any single node from becoming a performance bottleneck. This balanced distribution of tasks ensures optimal resource usage and performance. Moreover, distributed models enable dynamic resource allocation based on demand, allowing resources to be allocated and reallocated efficiently to meet changing workload requirements.
Improved Performance and Reliability
Apart from scalability, fault tolerance, and resource efficiency, distributed models also contribute to improved performance and reliability. By leveraging distributed computing techniques, organizations can achieve higher levels of system performance and reliability. The ability to distribute computing tasks across multiple nodes not only enhances system responsiveness but also reduces the risk of system failures, thereby ensuring a more reliable and robust infrastructure.
Flexibility and Adaptability
In addition to the core benefits of scalability, fault tolerance, efficient resource utilization, performance, and reliability, distributed models offer flexibility and adaptability. These models are designed to adapt to changing workloads and conditions seamlessly. With the ability to dynamically allocate resources, distributed systems can scale both vertically and horizontally, allowing for quick adjustments based on demand spikes or resource constraints. This adaptability ensures that the system can maintain optimal performance levels even during fluctuating operational conditions.
Cost-Effectiveness and Sustainability
Another advantage of distributed models lies in their cost-effectiveness and sustainability. By distributing workloads efficiently, organizations can optimize resource usage, leading to cost savings. Additionally, the redundancy built into distributed systems reduces the risk of catastrophic failures, enhancing system sustainability. This cost-effective and sustainable approach not only benefits the organization financially but also contributes to environmental sustainability by promoting efficient resource utilization.
The benefits of distributed models, including scalability enhancement, fault tolerance, efficient resource utilization, improved performance and reliability, flexibility and adaptability, as well as cost-effectiveness and sustainability, make them indispensable in modern cloud security architectures. By leveraging distributed models, organizations can build resilient, efficient, and future-proof systems that can adapt to the evolving demands of the digital landscape.
Challenges in Implementing Distributed Models
Complexity in Setup and Maintenance
Implementing distributed models often involves setting up and maintaining multiple interconnected systems, which can be complex and time-consuming. This complexity can arise from the need to ensure that all components are functioning correctly and communicating effectively. It is crucial to establish clear protocols and procedures for system updates, backups, and monitoring to minimize downtime and ensure smooth operations. Additionally, teams may require specialized training to navigate the intricacies of distributed systems efficiently.
Ensuring Data Consistency
Maintaining data consistency across distributed systems can be a significant challenge. With data stored and processed across multiple nodes, ensuring that all nodes have access to the most up-to-date and accurate information requires careful planning and implementation. Techniques such as distributed transactions, version control mechanisms, and data synchronization protocols are essential to mitigate inconsistencies and discrepancies that may arise due to network latency or node failures.
Addressing Security Concerns
Security is a paramount concern when implementing distributed models. With data being transmitted between nodes and potentially across networks, there is an increased risk of security breaches. Addressing security concerns requires implementing robust encryption, authentication, and access control measures to protect data and systems from unauthorized access and cyber threats. In addition to securing data in transit, it is vital to safeguard data at rest by employing encryption at the storage level and enforcing strict data access policies.
Scalability and Performance Optimization
Scalability is another key consideration in distributed model implementations. As the system grows, accommodating additional nodes and handling increased data volumes without compromising performance becomes crucial. Techniques such as horizontal scaling, load balancing, and caching mechanisms play a vital role in optimizing system performance and ensuring that the distributed model can scale seamlessly to meet evolving demands.
Fault Tolerance and Resilience
Ensuring fault tolerance and resilience is imperative in distributed systems to prevent single points of failure from causing system-wide disruptions. Implementing redundancy, failover mechanisms, and automated recovery procedures can help mitigate the impact of hardware failures, network outages, or other unforeseen events. By designing systems with resilience in mind, organizations can enhance system reliability and maintain continuous operations even in the face of adversity.
Monitoring and Management
Effective monitoring and management are essential components of successful distributed model implementations. By leveraging monitoring tools, organizations can track system performance, detect anomalies, and proactively address potential issues before they escalate. Implementing centralized management interfaces and automation capabilities streamlines the oversight of distributed systems, enabling efficient resource allocation, configuration management, and troubleshooting.
While implementing distributed models presents various challenges, organizations can overcome these obstacles by adopting a holistic approach that encompasses meticulous planning, robust security measures, scalability strategies, fault tolerance mechanisms, and effective monitoring practices. By addressing these challenges proactively and leveraging best practices, organizations can harness the potential of distributed models to drive innovation, enhance operational efficiency, and achieve sustainable growth in today’s dynamic digital landscape.
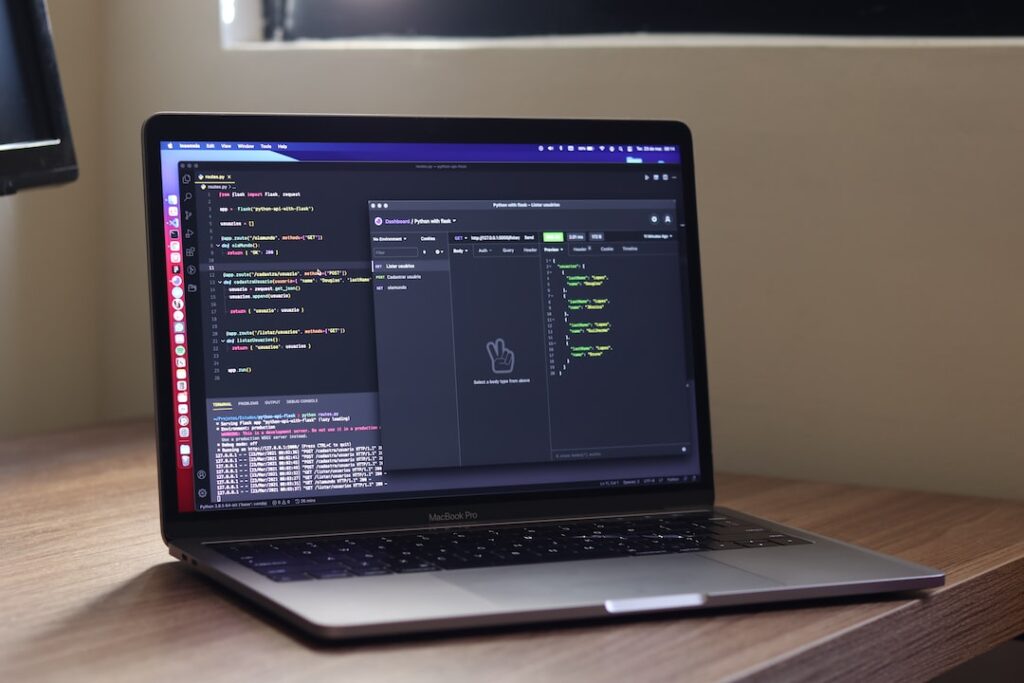
Best Practices for Successful Implementation
Successful implementation of robust security measures is crucial to safeguard sensitive data and ensure the integrity of systems. Let’s explore some key best practices that can bolster the security posture of your organization.
Advanced Encryption Techniques for Enhanced Security
Data security is a paramount concern for businesses in all industries. Implementing advanced encryption techniques such as end-to-end encryption, hashing, and data tokenization can significantly enhance the protection of your data. End-to-end encryption ensures that data is encrypted from the point of origin to the destination, making it indecipherable to unauthorized parties. Hashing converts sensitive information into unique strings of characters, adding an additional layer of security. Data tokenization replaces sensitive data with tokens, further reducing the risk of data exposure.
Continuous Monitoring and Auditing for Proactive Risk Management
Continuous monitoring and auditing are essential for maintaining the security of your systems. Regularly reviewing access logs, system activities, and user behaviors allows for the swift detection of anomalies or suspicious activities. Automated monitoring tools can offer real-time alerts for potential security breaches, enabling immediate mitigation actions. Conducting regular audits helps in evaluating compliance with security policies and regulations, facilitating timely adjustments to security protocols.
Effective Access Controls for Data Protection
Implementing robust access controls is vital in preventing unauthorized access to sensitive data. Role-based access control (RBAC) assigns permissions based on job roles, restricting access to information required for specific tasks. Multi-factor authentication (MFA) enhances security by requiring users to provide multiple forms of identification. Adhering to the principle of least privilege ensures that users only have access to the resources essential for their roles, minimizing the risk of data exposure.
By embracing these best practices and staying informed about emerging security trends, organizations can strengthen their defenses against cyber threats and safeguard valuable assets. Remember, proactive security measures are key to mitigating risks and maintaining a secure environment for your digital operations.
Real-world Applications and Case Studies
Success Stories of Companies Implementing Distributed Models.
Achievements in Security and Scalability.
The implementation of distributed models has revolutionized the way businesses operate. Companies across various industries have adopted these models to enhance their operations, improve efficiency, and drive innovation. Let’s delve into some success stories and case studies that highlight the impact of distributed models in the real world.
Success Stories of Companies Implementing Distributed Models
- Company A: Enhancing Customer Experience
Company A, a leading e-commerce platform, successfully implemented a distributed model to personalize customer experiences. By utilizing data analytics and distributed systems, they were able to recommend tailored products to customers, resulting in a significant increase in sales and customer satisfaction.
- Company B: Optimizing Supply Chain Management
Company B, a global logistics company, transformed its supply chain operations through the adoption of a distributed model. This enabled real-time tracking of shipments, streamlined inventory management, and improved overall operational efficiency. As a result, Company B saw a notable reduction in costs and delivery times.
Achievements in Security and Scalability
The implementation of distributed models has also led to significant advancements in security and scalability for businesses.
- Enhanced Security Measures
With distributed models, companies can improve data security by decentralizing storage and processing. This reduces the risk of a single point of failure and enhances protection against cyber threats. Several organizations have reported a decrease in security breaches after implementing distributed security measures.
- Scalability and Flexibility
Distributed models offer scalability and flexibility to businesses, allowing them to adapt to changing demands and scale operations seamlessly. Companies can easily expand their infrastructure and services without experiencing downtime or performance issues. This scalability has been crucial for businesses experiencing rapid growth and evolving market conditions.
Real-world Applications of Distributed Models
The real-world applications of distributed models extend beyond the success stories of individual companies. Industries such as finance, healthcare, and telecommunications have embraced distributed models to revolutionize their operations.
- Finance Industry
In the finance sector, distributed models have facilitated faster and more secure transactions. Blockchain technology, a form of distributed ledger, has enabled peer-to-peer transactions without the need for intermediaries, reducing costs and increasing transparency.
- Healthcare Sector
Healthcare institutions have leveraged distributed models to securely store and share patient data across different healthcare providers. This has improved the quality of care by ensuring that medical professionals have access to complete and up-to-date patient information.
- Telecommunications
Telecom companies have utilized distributed models to enhance network reliability and performance. By decentralizing network resources, these companies have been able to provide better connectivity and improved services to customers.
Future Trends and Challenges
Looking ahead, the adoption of distributed models is expected to continue growing. However, with this growth come challenges such as interoperability between different systems, data privacy concerns, and regulatory compliance. Companies will need to address these challenges to fully realize the benefits of distributed models.
The real-world applications and case studies of distributed models demonstrate their transformative impact on businesses. From enhancing customer experiences to improving security and scalability, companies are leveraging distributed models to drive innovation and stay competitive in today’s dynamic market landscape.
Future Perspectives and Trends in Cloud Security
The realm of cloud security is experiencing significant advancements and transformations. Two key factors driving these changes are the integration of artificial intelligence (AI) and machine learning for advanced threat detection capabilities, as well as a growing emphasis on privacy-preserving distributed models.
Integration of AI and Machine Learning for Threat Detection
The integration of AI and machine learning in cloud security is reshaping how organizations combat cyber threats. AI-driven threat detection systems are becoming increasingly sophisticated, enabling real-time monitoring, analysis, and response to potential security incidents. Machine learning algorithms can identify anomalies and patterns in vast amounts of data, enhancing the accuracy and efficiency of threat detection mechanisms. As cyber threats evolve in complexity, the synergy between AI and machine learning offers a proactive defense strategy for safeguarding cloud environments.
Focus on Privacy-Preserving Distributed Models
In response to growing concerns over data privacy and regulatory compliance, the adoption of privacy-preserving distributed models is gaining traction in cloud security strategies. These models prioritize data confidentiality by distributing processing tasks across multiple nodes, ensuring that sensitive information remains protected. By decentralizing data storage and computation, organizations can mitigate the risks associated with centralized data repositories and enhance the overall resilience of their security infrastructure. Privacy-preserving techniques such as homomorphic encryption and federated learning are facilitating secure data analysis while upholding individual privacy rights.
Evolving Security Challenges and Solutions
The landscape of cloud security is constantly evolving, presenting new challenges and opportunities for innovation. As cloud environments become more interconnected and complex, the need for adaptive security measures is paramount. Emerging technologies like quantum-resistant cryptography and zero-trust architectures are shaping the future of cloud security, offering robust defenses against emerging cyber threats. Additionally, the rise of edge computing and IoT devices necessitates a holistic approach to security, encompassing network segmentation, identity management, and continuous monitoring.
Looking ahead, the convergence of AI, machine learning, and privacy-preserving distributed models will drive continuous advancements in cloud security. Organizations must prioritize proactive risk management, invest in cybersecurity awareness and training, and collaborate with industry peers to stay ahead of evolving threats. By embracing a comprehensive security strategy that integrates cutting-edge technologies and best practices, businesses can fortify their defenses and ensure the resilience of their digital assets in an era of rapid digital transformation.
Conclusion
Leveraging distributed models in cloud security is essential for maximizing efficiency in today’s dynamic and complex digital landscape. By decentralizing security measures and spreading resources across multiple nodes, organizations can effectively mitigate risks, enhance scalability, and adapt to evolving threats. Embracing this approach not only bolsters overall security posture but also enables businesses to operate with agility and resilience in the face of modern cybersecurity challenges. As technology continues to advance, integrating distributed models into cloud security strategies will be paramount for staying ahead of cyber threats and safeguarding critical assets and data.