Achieving Role-Based Access Control (RBAC) Permission Inheritance

Achieving Role-Based Access Control (RBAC) permission inheritance is crucial for ensuring seamless access control within an organization’s systems and applications. By implementing RBAC, organizations can define and manage user permissions based on roles, enabling efficient assignment and revocation of access rights. Inheritance in RBAC allows for the propagation of permissions from higher-level roles to lower-level roles, simplifying the management process and ensuring consistency across the access control structure. This approach streamlines the administration of access rights, reduces the risk of errors, and enhances security by enforcing least privilege principles. Through RBAC permission inheritance, organizations can establish a hierarchical permission model that aligns with their organizational structure, facilitating granular control over user access while promoting scalability and flexibility. This introduction sets the stage for exploring the significance and benefits of RBAC permission inheritance in achieving robust access control mechanisms.
Understanding Permission Inheritance in RBAC
Definition of Permission Inheritance
Permission inheritance in Role-Based Access Control (RBAC) refers to the concept where permissions granted to a higher-level role are automatically passed down to lower-level roles and users within those roles. This means that if a role is granted certain permissions, all users assigned to that role will inherit those permissions by default.
Significance of Permission Inheritance in RBAC
-
Simplified Permission Management: By implementing permission inheritance, administrators can manage permissions at a higher level and ensure consistency across all users within the same role.
-
Reduced Administrative Overhead: With permission inheritance, the need to individually assign permissions to each user is eliminated, streamlining the administrative process and reducing the chances of errors.
-
Enhanced Security: Permission inheritance helps in enforcing the principle of least privilege by ensuring that users only have access to the resources necessary for their roles, reducing the risk of unauthorized access.
-
Scalability: As organizations grow and roles become more complex, permission inheritance enables efficient scaling by allowing new users to inherit the appropriate permissions based on their roles.
Implementation of Permission Inheritance
To implement permission inheritance effectively in RBAC, administrators need to carefully design role hierarchies. Understanding the relationships between different roles and defining clear inheritance rules is essential for a successful RBAC system. Additionally, regular reviews and updates to role permissions and inheritance structures are vital to adapt to organizational changes and ensure continued security.
Challenges and Best Practices
While permission inheritance offers numerous benefits, it also presents challenges such as potential over-entitlement and difficulty in managing complex inheritance structures. To address these challenges, organizations should regularly audit permissions, limit excessive inheritance levels, and provide training to administrators on proper role design and inheritance practices.
Future Trends
As cybersecurity threats evolve, the role of permission inheritance in RBAC is expected to become even more critical. Future trends may include the integration of artificial intelligence for automated permission management, dynamic permission inheritance based on user behavior analysis, and the incorporation of blockchain technology for secure permission delegation.
A thorough understanding of permission inheritance is essential for leveraging RBAC effectively in modern organizations. By embracing best practices, addressing challenges, and staying informed about emerging trends, administrators can build robust RBAC systems that enhance security, streamline operations, and adapt to the dynamic nature of access control requirements.
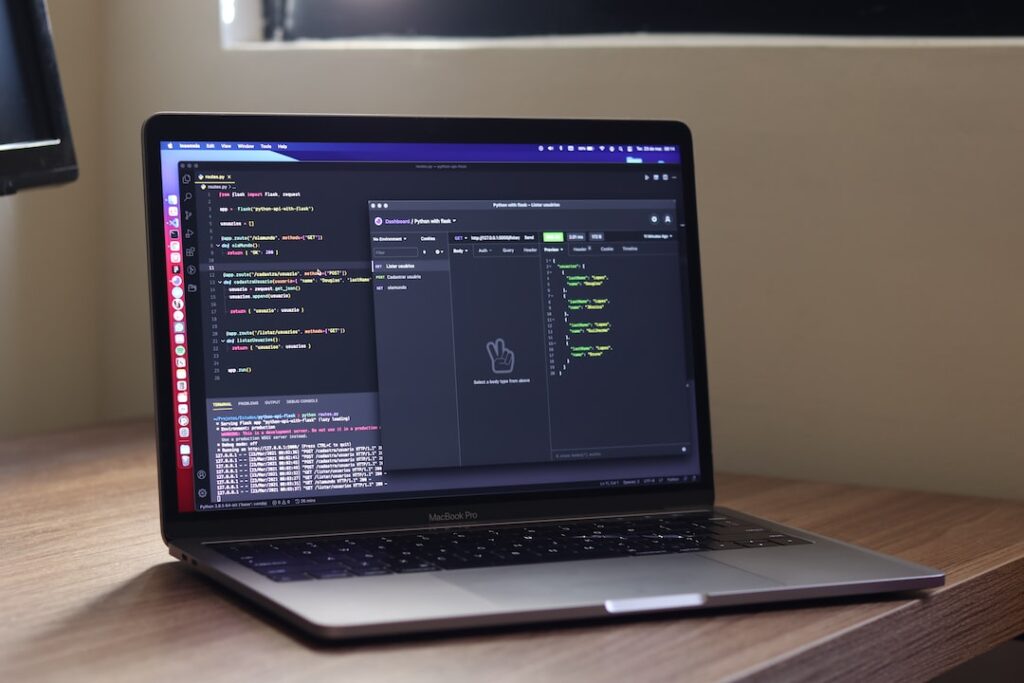
Implementing RBAC Permission Inheritance
Setting up Hierarchical Roles
In the realm of Role-Based Access Control (RBAC), setting up hierarchical roles is a foundational step towards establishing a robust access control framework. Hierarchical roles create a structured system where roles are organized in a hierarchy, enabling a systematic flow of permissions within an organization or system. By implementing hierarchical roles, businesses can streamline user management processes, improve scalability, and ensure a clear chain of command for permissions.
Defining Inheritance Rules
The definition of inheritance rules plays a pivotal role in ensuring the effective inheritance of permissions across different levels of roles in an RBAC system. Establishing well-defined inheritance rules is essential for maintaining consistency, enforcing security policies, and facilitating seamless access control operations. By clearly outlining how permissions cascade down the role hierarchy, organizations can enhance security and minimize the risk of unauthorized access.
Example Scenarios of Permission Inheritance
Examining example scenarios of permission inheritance can provide valuable insights into the practical implementation of RBAC systems. Consider scenarios where a user possesses overlapping roles with conflicting permissions. Implementing mechanisms like priority-based inheritance or rule-based conflict resolution mechanisms can help organizations address such conflicts effectively. By analyzing these scenarios, businesses can devise strategies to handle permission conflicts efficiently and ensure the proper management of access rights.
Role-Based Access Control Benefits
In addition to permission inheritance, RBAC offers numerous benefits that contribute to enhancing security, simplifying user management, and complying with regulatory standards. Through RBAC implementation, organizations can enforce the principle of least privilege, mitigate the risks of unauthorized access, and facilitate auditing and reporting processes to ensure compliance with data protection regulations.
Best Practices for RBAC Implementation
To optimize the effectiveness of RBAC, organizations should adhere to best practices such as conducting regular role reviews, optimizing role hierarchies, and continuously monitoring user permissions. Periodic role assessments, elimination of outdated roles, and vigilant monitoring of role assignments are crucial steps in maintaining the integrity of the access control framework and safeguarding against potential security threats.
Conclusion
The successful implementation of RBAC permission inheritance is vital for developing a secure and efficient access control system. By establishing hierarchical roles, defining clear inheritance rules, and addressing permission conflicts through strategic approaches, organizations can bolster their security posture, streamline user access processes, and uphold regulatory compliance standards.
Ensuring Seamless Access Control
Access control plays a crucial role in safeguarding sensitive data and resources within any organization. In this blog section, we will explore the significance of ensuring seamless access control and delve deeper into various best practices, the importance of regular auditing and monitoring, as well as the challenges and solutions associated with Role-Based Access Control (RBAC) implementation.
Role Assignment Best Practices
Role Assignment Best Practices: Ensuring proper role assignment is a foundational pillar of robust access control. Adhering to best practices when assigning roles to users is essential to guarantee that individuals have precisely the necessary access privileges. Implementing the principle of least privilege is key to minimizing the risks of unauthorized access attempts and potential security breaches. Additionally, incorporating role-based access control models can enhance security by grouping users based on job responsibilities and access needs.
Regular Auditing and Monitoring
Regular Auditing and Monitoring: Continuous auditing and monitoring of access control systems are critical to proactively detect and respond to any security incidents. By regularly reviewing access logs and conducting audits, organizations can swiftly identify unusual activities or unauthorized access attempts. This enables security teams to take immediate action to mitigate potential threats and strengthen access control measures.
Challenges and Solutions in RBAC Implementation
Challenges and Solutions in RBAC Implementation: While RBAC is a powerful access control model, its implementation can present challenges such as role explosion, role creep, and difficulties in managing roles across multiple systems. Overcoming these challenges requires meticulous planning, optimizing role hierarchies to prevent excessive permissions, and automating role assignment processes to streamline operations. Additionally, implementing continuous training and awareness programs for employees can help ensure proper understanding and adherence to access control policies.
Maintaining a seamless access control environment is essential for upholding the confidentiality, integrity, and availability of organizational assets. By following role assignment best practices, conducting regular audits, and effectively managing RBAC implementation challenges, businesses can fortify their security posture and mitigate potential risks effectively.
Conclusion
Implementing Role-Based Access Control (RBAC) permission inheritance is crucial for establishing a seamless access control mechanism within an organization. By ensuring that permissions are inherited hierarchically based on roles, organizations can streamline access management, reduce administrative overhead, and enhance security by enforcing consistent access policies across various levels of the organization. Embracing RBAC permission inheritance not only simplifies access control processes but also strengthens overall cybersecurity posture by eliminating potential gaps and reducing the risk of unauthorized access. It is evident that integrating RBAC permission inheritance is a strategic move for organizations looking to enhance operational efficiency, compliance, and data protection in today’s dynamic and evolving digital landscape.