Protecting Sensitive Information in the Digital Age

Protecting sensitive information is paramount. Enhancing data privacy through effective masking strategies is crucial to safeguarding personal and confidential data from unauthorized access. Data masking involves disguising data by replacing, encrypting, or shuffling elements to ensure its confidentiality while retaining its usability for authorized purposes. This proactive approach helps organizations comply with data privacy regulations, mitigate data breaches, and build trust with customers. By implementing robust masking techniques, such as tokenization, encryption, and anonymization, businesses can minimize the risk of data exposure and protect sensitive information across various touchpoints. As technology advances and cyber threats evolve, the significance of data privacy continues to grow, making it essential for businesses to prioritize data masking as a fundamental aspect of their security strategy.
Fundamentals of Data Masking
Explanation and Purpose of Data Masking
Data masking, also known as data obfuscation or data anonymization, is a critical practice employed to secure sensitive information. Where the volume of data collected and stored is rapidly increasing, protecting confidential data from unauthorized access is paramount. Data masking involves modifying sensitive data in a way that it remains usable for various purposes but without exposing the actual details. The primary objective of data masking is to ensure data privacy and security by preventing unauthorized exposure or misuse of confidential information.
Common Techniques Used for Data Masking
- Substitution: This method involves replacing real data with fictitious yet plausible values to maintain data integrity while concealing sensitive information effectively.
- Shuffling: By rearranging the sequence of data records, shuffling makes it difficult to link specific data elements to individuals, thereby enhancing privacy protection.
- Masking: Masking conceals parts of sensitive data by substituting them with symbols like X or •, ensuring that the original information remains hidden from unauthorized viewers.
- Encryption: Data encryption converts information into an unreadable format that can only be deciphered using the appropriate decryption key, providing an additional layer of security.
- Tokenization: Tokenization replaces sensitive data with unique tokens, which are randomly generated values that have no relationship to the original data, thereby protecting the confidentiality of information.
Benefits of Implementing Data Masking
- Enhanced Data Privacy: Implementing data masking techniques helps organizations maintain the confidentiality of sensitive information, reducing the risk of unauthorized exposure and ensuring data privacy.
- Regulatory Compliance: Data masking aids companies in complying with stringent data protection regulations such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA), thereby avoiding potential legal consequences.
- Risk Mitigation: By masking sensitive data, organizations can lower the probability of data breaches, leaks, or misuse, thereby safeguarding their reputation and maintaining trust with customers and stakeholders.
- Data Utilization Flexibility: Data masking allows organizations to share information for testing, training, or analysis purposes without compromising the security of sensitive details. This flexibility promotes data-driven decision-making and innovation while upholding strict data security standards.
- Scalability and Performance: Implementing efficient data masking solutions ensures scalability and high performance, enabling organizations to protect data across various environments and applications without impacting operational efficiency.
- Cost-Efficiency: Data masking solutions offer cost-effective ways to secure sensitive data, reducing the expenses associated with data breaches and regulatory non-compliance.
Data masking is a vital strategy for safeguarding sensitive information in an increasingly interconnected world. By understanding the fundamentals of data masking, organizations can enhance data security, ensure regulatory compliance, mitigate risks, and foster innovation while maintaining data privacy and confidentiality.
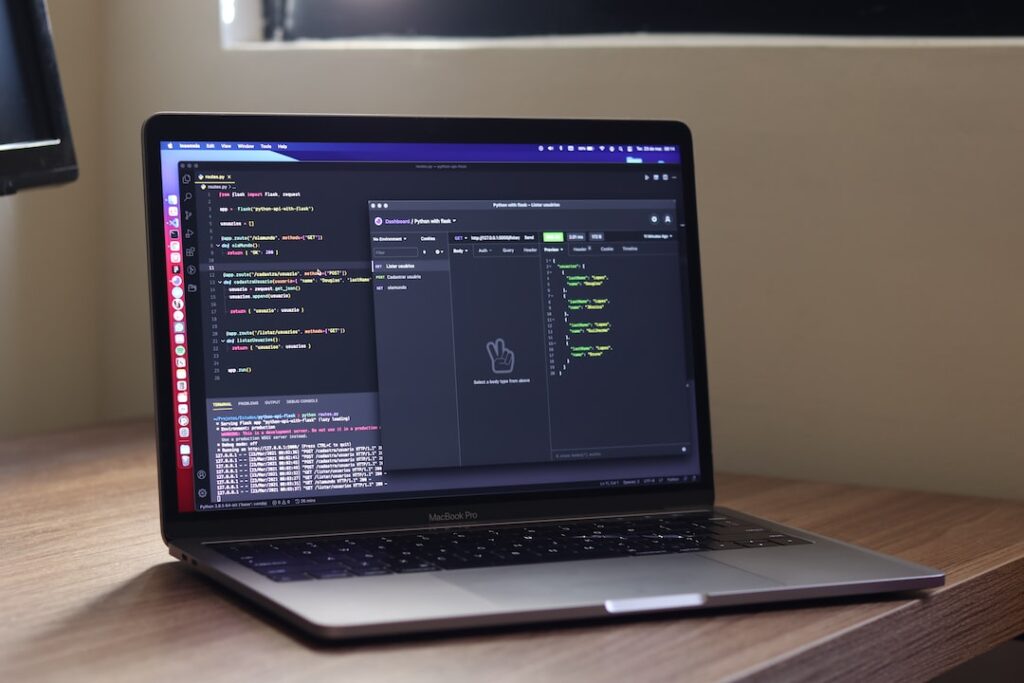
Effective Implementation of Masking Techniques
Key Considerations Before Applying Data Masking
When it comes to implementing data masking techniques, there are several key considerations that organizations need to keep in mind. Understanding the sensitivity of the data being masked is crucial. It’s essential to identify what specific data elements need to be masked to protect sensitive information effectively. By conducting a thorough assessment of the data and potential risks involved, organizations can tailor their masking strategy to meet their unique requirements.
Integration of Masking with Data Security Measures
Data masking should not be seen as a standalone solution but rather as an integral part of a broader data security strategy. To enhance the overall protection of sensitive data, organizations should integrate masking techniques with other security measures such as encryption, access controls, and monitoring tools. This layered approach can significantly reduce the risk of data breaches and unauthorized access.
Addressing Compliance Requirements through Masking
Compliance with industry regulations and data protection laws is of utmost importance. Many regulatory frameworks mandate the use of data masking to safeguard sensitive information. By effectively applying masking techniques, organizations can demonstrate compliance with these requirements and mitigate the risk of non-compliance-related penalties and reputational damage.
Best Practices for Data Masking
To ensure the effectiveness of data masking, organizations should follow a set of best practices. This includes regularly reviewing and updating masking policies to align with changing data privacy regulations and evolving security threats. Additionally, implementing robust access controls and monitoring mechanisms can help detect any unauthorized attempts to access masked data.
Advantages of Dynamic Data Masking
Dynamic data masking is a technique that provides real-time data obfuscation to prevent unauthorized access to sensitive information. By dynamically masking data based on user roles or access privileges, organizations can control the level of data exposure and ensure that only authorized personnel can view sensitive information.
Challenges in Implementing Data Masking
While data masking is a powerful tool for protecting sensitive data, organizations may encounter challenges during implementation. Issues such as maintaining data consistency across different environments, ensuring performance efficiency, and managing access to masked data can pose obstacles. It’s essential for organizations to address these challenges proactively to maximize the effectiveness of their masking strategies.
Future Trends in Data Masking
As data privacy regulations continue to evolve and cyber threats become more sophisticated, the field of data masking is also advancing. Future trends in data masking may include the integration of artificial intelligence for automated masking, the development of more granular masking techniques to protect specific data elements, and increased focus on data residency and sovereignty requirements. Staying abreast of these trends can help organizations adapt their masking strategies to meet emerging security challenges.
Conclusion
Effective implementation of data masking techniques is essential for safeguarding sensitive information and maintaining regulatory compliance. By carefully considering key factors, integrating masking with other security measures, and following best practices, organizations can enhance their data protection capabilities and reduce the risk of data breaches. With the continuous evolution of data privacy regulations and security threats, staying proactive and adaptive in data masking practices is crucial for ensuring the confidentiality and integrity of sensitive data.
Real-world Applications of Data Masking
In the digital age, where data breaches and privacy concerns are rampant, the practice of data masking has emerged as a crucial tool to safeguard sensitive information. Data masking involves the process of obfuscating or hiding data elements to protect their confidentiality while retaining their format and usability for specific purposes. This blog section explores the real-world applications of data masking, delving into case studies that demonstrate successful masking strategies and examining the profound impact of data masking on privacy and security.
Case Studies Demonstrating Successful Masking Strategies
Healthcare Industry
Data masking plays a pivotal role in the healthcare industry, where patient records contain highly sensitive information such as medical history, diagnoses, and treatment plans. By implementing data masking techniques, healthcare organizations can anonymize patient data for use in research, analytics, and software testing without compromising individuals’ privacy. Case studies have shown that data masking not only ensures compliance with regulations like HIPAA but also enhances data security across the healthcare ecosystem.
Financial Sector
In the financial sector, data masking is instrumental in protecting customer financial information, account details, and transaction records from unauthorized access. By masking sensitive data elements like credit card numbers, social security numbers, and account balances, financial institutions can mitigate the risk of financial fraud and identity theft. Real-world examples have illustrated how data masking solutions have bolstered data protection measures, enabling seamless data sharing for business operations while upholding strict security protocols.
Impact of Data Masking on Privacy and Security
Preserving Confidentiality
One of the primary benefits of data masking is its ability to preserve confidentiality by concealing sensitive information from unauthorized users. Whether in databases, test environments, or cloud storage, masked data ensures that only authorized personnel can access and utilize the original data, safeguarding against breaches and leaks.
Mitigating Risks
Data masking serves as a proactive measure to mitigate risks associated with data exposure and cyber threats. By masking personally identifiable information (PII) and other critical data points, organizations reduce the likelihood of data breaches, identity theft, and regulatory non-compliance, fostering a secure data environment.
Enabling Compliance
Data masking aids in achieving regulatory compliance by anonymizing sensitive data in accordance with data protection laws and industry standards. Through effective masking strategies, businesses can adhere to regulations like GDPR, PCI DSS, and SOX while leveraging data for analytics, reporting, and research purposes.
The real-world applications of data masking extend far beyond mere data protection; they encompass a holistic approach to privacy, security, and regulatory adherence in an increasingly data-driven landscape. By exploring case studies and understanding the impact of data masking, organizations can fortify their data defenses and instill trust among stakeholders in an era where data privacy is paramount.
Challenges and Solutions in Masking Adoption
Obstacles Encountered When Implementing Masking
Implementing data masking can present certain challenges that organizations need to overcome to ensure the security and privacy of sensitive information. Some common obstacles include:.
-
Complexity of Data Ecosystem : Managing data across various platforms and systems can complicate the implementation of masking techniques.
-
Performance Impact : Introducing data masking can sometimes impact system performance, causing delays in data processing.
-
Compliance Requirements : Meeting regulatory standards such as GDPR and HIPAA adds an additional layer of complexity to data masking implementation.
-
Data Accuracy : Masking data while maintaining accuracy can be a challenge, as certain masking techniques may alter the data in a way that affects its usability.
Effective Strategies to Overcome Masking Challenges
To address the challenges associated with data masking adoption, organizations can implement the following strategies:.
-
Comprehensive Data Discovery : Conduct a thorough assessment to identify all sensitive data that needs to be masked.
-
Prioritize Data Elements : Focus on masking the most critical data elements first to ensure maximum protection.
-
Testing and Validation : Regularly test and validate the effectiveness of masking techniques to identify and address any issues.
-
Employee Training : Provide training to staff members involved in data masking to ensure proper implementation and adherence to policies.
-
Dynamic Masking Solutions : Explore advanced masking solutions that offer dynamic data masking capabilities, allowing for real-time protection of sensitive information.
-
Integration with Data Governance : Integrate data masking processes with overall data governance strategies to ensure alignment with data privacy and security objectives.
-
Continuous Monitoring : Establish processes for continuous monitoring of masked data to detect any unauthorized access or breaches.
Implementing data masking is crucial for protecting sensitive information, but organizations often face challenges during the adoption process. Beyond the previously mentioned obstacles, other common issues may arise, such as resource constraints and the need for specialized expertise in implementing complex masking algorithms effectively.
One effective approach to overcoming these challenges is to engage with third-party experts or consultants who specialize in data security and privacy. These professionals can provide valuable insights, best practices, and guidance on selecting the most suitable data masking solutions for specific organizational needs.
Moreover, staying informed about emerging trends and advancements in data masking technologies is essential for ensuring that organizations stay ahead of potential security threats. Continuous education and professional development for internal teams involved in data masking can further enhance the efficacy of data protection measures.
While challenges in data masking adoption are prevalent, proactive planning, strategic partnerships, and a commitment to ongoing improvement are key to successfully implementing and maintaining robust data masking practices. By addressing obstacles head-on and embracing innovative solutions, organizations can strengthen their data security posture and safeguard sensitive information effectively.
Future Trends in Data Privacy and Masking
Data privacy and masking have become crucial aspects of protecting sensitive information. With the rapid advancements in technology, it is essential to stay updated on the future trends that will shape the landscape of data privacy and masking practices. Let’s explore two key points that highlight the emerging technologies impacting data masking practices and predictions for the evolution of data privacy.
Emerging Technologies Shaping Data Masking Practices
-
Artificial Intelligence and Machine Learning in Data Masking: The integration of AI and ML algorithms in data masking solutions is revolutionizing how organizations protect their data. These technologies enable automated data masking processes, making it easier to secure large volumes of sensitive information effectively. AI and ML not only streamline the data masking process but also enhance the accuracy and efficiency of identifying and protecting sensitive data elements.
-
Blockchain for Enhanced Data Privacy: Blockchain technology is being leveraged to enhance data privacy by providing a secure and transparent way to store and share information. Its decentralized nature makes it difficult for unauthorized parties to access or tamper with sensitive data, thereby strengthening privacy measures. Additionally, blockchain’s immutable ledger ensures data integrity, enhancing trust among data users and minimizing the risk of data breaches or unauthorized access.
Predictions for the Evolution of Data Privacy
-
Increased Focus on Privacy Regulations: As data privacy concerns continue to rise, there will be a greater emphasis on regulatory compliance. Organizations will need to adapt to evolving privacy laws and regulations to ensure they are effectively safeguarding customer data and maintaining trust. The implementation of robust data privacy policies and compliance frameworks will be essential to mitigate data privacy risks and avoid regulatory penalties.
-
Adoption of Privacy-Enhancing Technologies: With the growing demand for enhanced data privacy, there will be a surge in the adoption of privacy-enhancing technologies. From advanced encryption methods to secure data sharing protocols, businesses will invest in innovative solutions to protect sensitive information. Additionally, the integration of privacy-preserving technologies such as differential privacy and homomorphic encryption will enable organizations to maximize data utility while preserving individual privacy.
-
Rise of Privacy by Design: Privacy by design principles will gain prominence as organizations prioritize embedding privacy features into their products and services from the initial design phase. By incorporating privacy controls and data protection measures into the core architecture of systems and applications, companies can proactively address privacy risks and enhance user trust.
The future of data privacy and masking is poised for significant advancements driven by emerging technologies and changing regulatory landscapes. By staying informed and proactive, organizations can navigate these trends to safeguard their data effectively and maintain consumer trust in an increasingly data-driven world.
Conclusion
Implementing effective data masking strategies is crucial in enhancing data privacy and protecting sensitive information. By utilizing techniques such as tokenization, encryption, and obfuscation, organizations can safeguard their data from unauthorized access and mitigate the risk of data breaches. Prioritizing data privacy not only ensures regulatory compliance but also builds trust with customers and stakeholders. It is imperative for businesses to continuously assess and improve their data masking practices to stay ahead of evolving cybersecurity threats and safeguard valuable data assets.