In the realm of cybersecurity, understanding and implementing effective permission inheritance models are crucial for ensuring robust security practices. This exploration delves into the various permission inheritance models that organizations can adopt to enhance their security posture. By investigating how permissions are inherited within different systems and platforms, businesses can tailor their access control strategies to mitigate risks and safeguard sensitive data. Through this examination, we aim to shed light on the significance of permission inheritance in bolstering overall security frameworks. Join us as we navigate through the intricacies of permission inheritance models, unraveling the complexities to pave the way for improved security protocols and heightened data protection.
Types of Permission Inheritance Models
Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is a method of restricting network access based on the roles of individual users within an enterprise. RBAC assigns permissions to roles, not individual users, making it easier to manage user permissions. This model is widely used in organizations to enforce strict access controls.
Mandatory Access Control (MAC)
Mandatory Access Control (MAC) is a security model in which access rights are regulated by a central authority based on multiple levels of security. Users do not have control over their access permissions, as they are set by the system administrator. MAC is commonly used in government and military environments where data confidentiality is crucial.
Discretionary Access Control (DAC)
Discretionary Access Control (DAC) is a model in which the owner of the resource has full control over who can access the resource and what actions they can perform. Unlike MAC, where access control is enforced by the system, in DAC, the owner of the resource determines who can access it. This model is more flexible but can also lead to security risks if permissions are not managed properly.
Comparison of Models
While all three models play vital roles in access control, they differ in their implementation and level of control. RBAC simplifies user permissions management by grouping users based on their roles, but it might lack the granularity provided by MAC or DAC. MAC enforces strict hierarchical access control, suitable for environments where data integrity is paramount, while DAC offers more flexibility but requires careful management to prevent unauthorized access.
Real-World Applications
RBAC is commonly used in business environments to streamline access management and reduce the risk of unauthorized data exposure. In contrast, MAC is prevalent in government sectors, ensuring that sensitive information remains protected at all times. DAC finds its applications in scenarios where resource owners need direct control over access, such as file systems on personal computers.
Emerging Trends
With the evolving landscape of cybersecurity, the integration of these models into comprehensive access control frameworks is gaining traction. Hybrid models combining aspects of RBAC, MAC, and DAC are being developed to address the varying needs of modern organizations, offering a balanced approach between strict control and user flexibility.
Conclusion
Understanding the nuances of Role-Based Access Control, Mandatory Access Control, and Discretionary Access Control is crucial for designing robust security measures in today’s digital age. By leveraging the strengths of each model and adapting them to specific use cases, organizations can establish effective access control strategies that safeguard their data and systems from potential threats.
Comparison of Different Permission Inheritance Models
Role-Based Access Control (RBAC): Key Features and Use Cases
Role-Based Access Control (RBAC) is a widely used permission inheritance model that assigns access rights based on roles and responsibilities within an organization. Key features of RBAC include role hierarchies, role assignment, role authorization, and role permissions. Use cases for RBAC include large organizations with complex access control needs, such as healthcare institutions, financial organizations, and government agencies.
Mandatory Access Control (MAC): Strengths and Weaknesses
Mandatory Access Control (MAC) is a stringent access control model where access rights are determined by the system and cannot be changed by users or administrators. Strengths of MAC include high security levels, centralized control, and protection of sensitive data. However, weaknesses of MAC include inflexibility, complexity in implementation, and potential for user frustration due to restricted permissions.
Discretionary Access Control (DAC): Advantages and Limitations
Discretionary Access Control (DAC) is a more flexible permission model where users have control over their objects and can grant or revoke access to others. Advantages of DAC include simplicity, user autonomy, and ease of implementation. However, limitations of DAC involve security risks due to potential user error, lack of centralized control, and challenges in managing access rights in large organizations.
Comparing RBAC, MAC, and DAC
While RBAC, MAC, and DAC are distinct permission inheritance models, a comparative analysis can help organizations make informed decisions regarding the most suitable model for their specific needs. RBAC offers structured access control through predefined roles, making it ideal for organizations with well-defined hierarchies and clear role responsibilities. On the other hand, MAC provides a high level of security by strictly enforcing access rules set by the system, making it suitable for environments handling highly sensitive information where user discretion must be limited.
DAC, with its user-centric approach, empowers individuals to manage their access permissions, fostering a sense of ownership and flexibility. However, this freedom comes with inherent risks, especially in environments where data security is paramount. Organizations must weigh the benefits and drawbacks of each model to strike a balance between security, usability, and administrative complexity.
The choice between RBAC, MAC, and DAC should be guided by a thorough understanding of the organization’s security requirements, operational structure, and data sensitivity. By selecting the most appropriate permission inheritance model, organizations can establish robust access control mechanisms that align with their unique needs and safeguard critical assets effectively.
Best Practices for Implementing Permission Inheritance Models
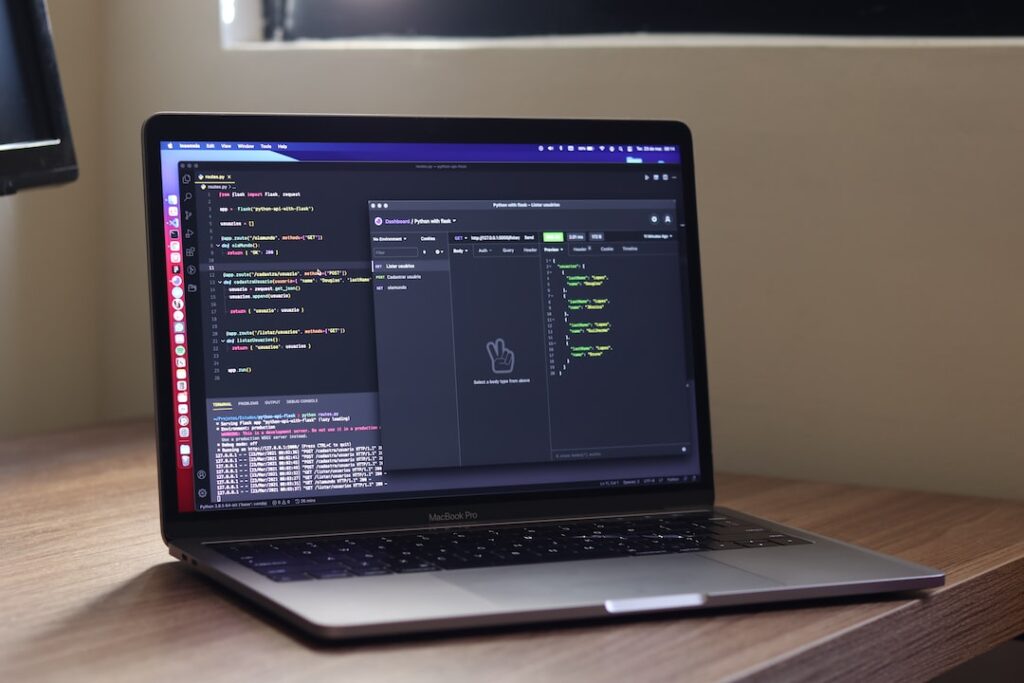
Role Definition and Assignment Strategies
In the realm of implementing permission inheritance models, establishing effective role definition and assignment strategies is crucial for ensuring the security and efficiency of access control. Well-defined roles should encompass a clear delineation of permissions specific to each role. Assigning roles based on job responsibilities, hierarchy, and access requirements guarantees that individuals have the necessary privileges to fulfill their duties while maintaining data security.
Regular Auditing and Monitoring Protocols
An indispensable aspect of maintaining a robust permission inheritance model is the implementation of regular auditing and monitoring protocols. Periodic audits play a pivotal role in verifying the accuracy and appropriateness of permissions assigned. By monitoring access logs, detecting unusual activities, and promptly addressing unauthorized access attempts, organizations can uphold data integrity and fortify their security posture.
Integration with Security Policies
The seamless integration of permission inheritance models with overarching security policies is paramount for a comprehensive security framework. Adhering to data sensitivity levels, industry regulations, and best practices ensures that permissions are aligned with organizational security objectives. Continuously reviewing and updating security policies to reflect emerging threats and compliance standards is essential for safeguarding sensitive information.
Access Revocation Procedures
Establishing well-defined procedures for access revocation is a critical component of permission inheritance models. Swift adjustment or revocation of permissions is imperative when individuals undergo role changes or depart from the organization to prevent unauthorized access. Leveraging automated tools for access management streamlines this process, minimizing the risk of oversight or unauthorized access.
Training and Awareness Programs
Educating users on the significance of permissions and the risks associated with improper access is pivotal for fostering a security-conscious culture. Implementing comprehensive training programs that emphasize security best practices, data protection protocols, and the repercussions of unauthorized access cultivates a workforce that values data security and compliance.
Continuous Improvement Initiatives
Sustaining the efficacy of permission inheritance models necessitates a commitment to continuous improvement. Soliciting feedback from users, conducting regular security assessments, and implementing enhancements based on audit findings and incident response evaluations empower organizations to adapt proactively to evolving security challenges and operational needs. Embracing a culture of continuous improvement fosters resilience and agility in addressing emerging threats.
Future Trends in Permission Inheritance Models
The traditional methods of permission inheritance models are being reshaped by innovative technologies and approaches. One of the key future trends in this area is the adoption of Adaptive Access Control Systems. These systems utilize dynamic policies and contextual information to make real-time access decisions, ensuring that permissions are granted based on the current scenario rather than predefined rules.
Additionally, Machine Learning is playing a significant role in revolutionizing permission management. By leveraging algorithms that can analyze patterns and behaviors, organizations can automate the process of assigning and adjusting permissions. This not only enhances security by detecting anomalies but also improves efficiency by reducing the manual effort required for permission management.
As we look ahead, it is evident that the future of permission inheritance models will be shaped by the integration of technologies like Adaptive Access Control Systems and Machine Learning. These advancements promise not only enhanced security but also more streamlined and intelligent permission management processes.
Adaptive Access Control Systems
Adaptive Access Control Systems are at the forefront of reshaping how permissions are managed in organizations. These systems go beyond traditional static permission models by dynamically adapting access based on real-time context. For example, if a user’s behavior suddenly deviates from the norm, the system can automatically adjust permissions to mitigate potential risks. This proactive approach enhances security and reduces the likelihood of unauthorized access.
Machine Learning in Permission Management
The integration of Machine Learning algorithms in permission management brings a new level of intelligence to the process. Machine Learning can analyze vast amounts of data to identify patterns and anomalies that human administrators might miss. By continuously learning from user interactions and access patterns, Machine Learning algorithms can optimize permissions, ensuring that users have the right level of access at all times. This not only strengthens security but also simplifies the management of complex permission structures.
Looking to the future, the combination of Adaptive Access Control Systems and Machine Learning in permission inheritance models holds great promise for organizations seeking to enhance their security posture and operational efficiency. By embracing these advanced technologies, businesses can stay ahead of evolving threats and adapt quickly to changing access requirements.
Exploring different permission inheritance models
Exploring different permission inheritance models is crucial for enhancing security measures within an organization. By understanding and implementing the most suitable model, businesses can ensure that access rights are granted appropriately and securely across various levels of their systems. Ultimately, this proactive approach can lead to a more robust security framework, safeguarding sensitive information from potential breaches and unauthorized access.