Where the interconnectedness of systems and applications is ubiquitous, ensuring the security of pipelines that facilitate data flow is paramount. Pipeline hardening, a vital aspect of cybersecurity, focuses on fortifying the APIs and integrations that form the backbone of these data conduits. By implementing robust security measures at every stage of the pipeline, organizations can mitigate the risks of data breaches, unauthorized access, and other cyber threats. This proactive approach not only safeguards sensitive information but also fosters trust among users and partners. In this era of relentless cyberattacks and evolving threats, the significance of pipeline hardening cannot be overstated. Join us as we delve into the intricacies of strengthening API and integration security, exploring best practices, emerging trends, and practical strategies to bolster the resilience of your digital pipelines.
Analyzing Vulnerabilities in Pipelines
Common Weaknesses
Pipelines play a crucial role in ensuring the smooth delivery of code from development to production. However, these pipelines are often susceptible to various vulnerabilities that can be exploited by malicious actors. Understanding the common weaknesses in pipelines is key to enhancing security measures.
Lack of Proper Authentication
One of the most common weaknesses found in pipelines is the lack of proper authentication mechanisms. Without strong authentication protocols in place, pipelines are at risk of unauthorized access, allowing attackers to manipulate the code or inject malicious scripts.
Inadequate Encryption
Another critical weakness is inadequate encryption of data within pipelines. Failure to encrypt sensitive information such as passwords or API keys can lead to data breaches and compromise the entire pipeline process.
Vulnerable Dependencies
Pipelines rely on various dependencies and third-party libraries, making them vulnerable to attacks if these dependencies are not regularly updated or contain security flaws. It is essential to continuously monitor and update dependencies to mitigate potential risks.
Impact of Security Breaches
Security breaches in pipelines can have far-reaching consequences, affecting not only the development process but also the overall integrity of the software being delivered. Understanding the impact of security breaches is crucial for organizations to prioritize security measures and protect their pipelines.
Delay in Delivery
A security breach can result in a significant delay in the delivery of code, disrupting the development timeline and potentially affecting project deadlines. This delay not only impacts the development team but also the end-users awaiting new features or updates.
Data Compromise
Perhaps the most severe impact of a security breach is the compromise of sensitive data. In pipelines, data such as user information, credentials, or intellectual property can be exposed, leading to legal consequences and reputational damage for the organization.
Loss of Trust
Security breaches not only impact the technical aspects of software development but also erode trust among stakeholders, including customers, partners, and investors. A breach in the pipeline’s security can tarnish the organization’s reputation and lead to loss of trust in its products and services.
Analyzing vulnerabilities in pipelines and understanding the potential impact of security breaches are essential steps in strengthening the security posture of software development processes. By addressing common weaknesses and implementing robust security measures, organizations can better protect their pipelines and safeguard their valuable assets.
Strategies for Strengthening API and Integration Security
Where data is constantly shared between various applications and systems, ensuring the security of APIs and integrations is paramount for safeguarding sensitive information and maintaining the trust of users and stakeholders. While the benefits of APIs in enabling seamless communication between different software components are undeniable, they also introduce potential vulnerabilities that malicious actors can exploit. Therefore, implementing robust security measures is crucial to mitigate risks and protect valuable data.
One of the fundamental strategies for strengthening API and integration security is to enforce secure authentication mechanisms. By employing methods like OAuth, API keys, or token-based authentication, organizations can verify the identity of users and applications accessing their APIs, reducing the likelihood of unauthorized access. Additionally, implementing strong data encryption techniques such as SSL/TLS protocols ensures that information exchanged between systems remains confidential and protected from eavesdropping or tampering.
Continuous monitoring and testing play a vital role in identifying and addressing security weaknesses in APIs and integrations. Regular security assessments, penetration testing, and vulnerability scanning help organizations proactively detect and remediate potential threats before they can be exploited. By staying vigilant and responsive to emerging security risks, businesses can maintain the integrity and resilience of their API ecosystem.
Furthermore, adopting a security-first approach in API development involves prioritizing security considerations at every stage of the development lifecycle. This includes conducting thorough risk assessments, implementing least privilege access controls, and incorporating security best practices into the design and implementation of APIs. By building security controls directly into the API architecture, organizations can reduce the likelihood of security breaches and data leaks.
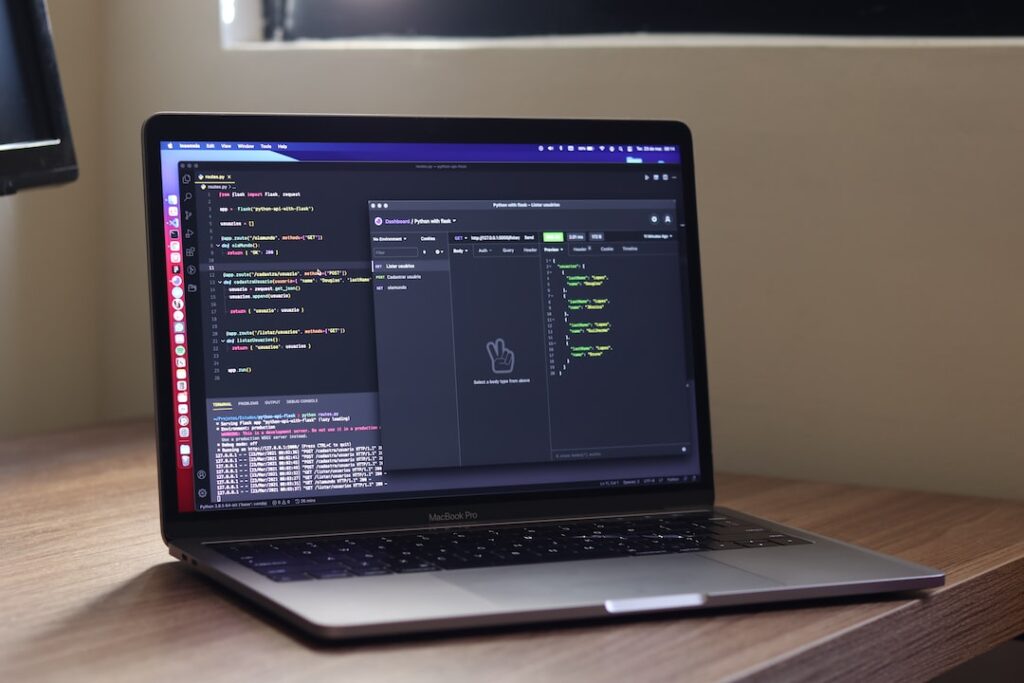
Integrating continuous integration and deployment pipelines into the development process can also enhance API security by automating security checks, code reviews, and testing procedures. By streamlining the delivery of secure code updates and patches, teams can ensure that APIs remain resilient to evolving cyber threats and compliance requirements.
A comprehensive approach to API and integration security involves a combination of proactive security measures, rigorous testing, and ongoing monitoring to safeguard digital assets and uphold trust in the digital ecosystem. By prioritizing API quality assurance, leveraging industry best practices, and partnering with security experts like CloudSecurityWeb, organizations can fortify their APIs against potential threats and build a foundation of trust and reliability in their digital offerings.
Best Practices for Pipeline Hardening
Role-Based Access Control
Role-based access control (RBAC) plays a pivotal role in ensuring the security and integrity of pipeline infrastructure. By defining and enforcing specific roles and permissions for individuals or groups within an organization, RBAC limits access to sensitive pipeline components only to authorized personnel. This not only minimizes the risk of unauthorized access but also mitigates the potential for security breaches and data leaks.
Regular Security Audits and Updates
To maintain a robust pipeline security posture, regular security audits and updates are paramount. By conducting frequent audits, organizations can proactively identify vulnerabilities or weaknesses in their pipeline architecture and promptly address them. Moreover, staying vigilant with software and tool updates is crucial in safeguarding against known security vulnerabilities and exploits. Implementing a proactive approach to security maintenance ensures that the pipeline remains resilient to emerging threats and attack vectors.
Incident Response Planning
An effective incident response plan is indispensable for organizations seeking to fortify their pipeline against security threats. Establishing a comprehensive incident response plan enables swift and coordinated responses to security incidents or breaches. The plan should delineate clear protocols for incident containment, forensic investigation, system recovery, and communication strategies to stakeholders. By rehearsing and refining incident response procedures, organizations can enhance their readiness to mitigate security incidents and minimize potential disruptions to pipeline operations.
Continuous Monitoring and Threat Intelligence Integration
In addition to the fundamental practices mentioned above, integrating continuous monitoring and threat intelligence feeds into the pipeline security framework can significantly enhance threat detection and response capabilities. By leveraging real-time monitoring tools and threat intelligence sources, organizations can proactively identify suspicious activities, anomalous behavior, or emerging threats within their pipeline environment. This proactive stance empowers organizations to preemptively thwart potential security incidents and bolster the overall resilience of their pipeline infrastructure.
Conclusion
Implementing a comprehensive security strategy that encompasses role-based access control, regular security audits, incident response planning, continuous monitoring, and threat intelligence integration is imperative for pipeline hardening. By adhering to these best practices and remaining vigilant against evolving security threats, organizations can fortify their pipeline infrastructure and uphold the confidentiality, integrity, and availability of critical data and resources.
Conclusion
Investing in pipeline hardening to strengthen API and integration security is crucial in today’s digital landscape. By implementing robust security measures, organizations can better protect their systems, data, and users from potential threats and vulnerabilities. It is essential to continuously evaluate and enhance security protocols to stay ahead of cyber threats and ensure a secure environment for all stakeholders involved. With a proactive approach to pipeline hardening, organizations can mitigate risks and build a strong defense against malicious activities targeting their APIs and integrations.