Protecting sensitive data is paramount to safeguarding individuals’ privacy and preventing data breaches. One crucial aspect of this is implementing effective Personally Identifiable Information (PII) masking strategies. PII encompasses any data that could potentially identify a specific individual, such as social security numbers, addresses, or financial information. By employing robust PII masking techniques, organizations can obscure or encrypt sensitive data to ensure that even if a breach occurs, the exposed information remains unintelligible and unusable to unauthorized parties. This not only helps in compliance with data protection regulations like GDPR and CCPA but also builds trust with customers by demonstrating a commitment to data security and privacy. In this context, exploring various PII masking approaches, such as tokenization, encryption, or data anonymization, becomes crucial for organizations across industries to fortify their data protection measures and mitigate the risks associated with handling sensitive information.
Challenges in Data Security
Common Threats to Data Security
Safeguarding data has become paramount due to the escalating risks posed by cyber threats. Understanding and addressing these risks is crucial for individuals and businesses striving to protect their sensitive information.
Phishing Attacks
Phishing attacks remain a prevalent threat to data security. Cybercriminals use deceptive tactics, such as fraudulent emails or websites, to trick individuals into divulging confidential data like login credentials or financial details. Vigilance and awareness are key in combating this insidious threat.
Malware
The proliferation of malware, encompassing viruses, worms, and ransomware, continues to jeopardize data integrity. These malicious programs can infiltrate systems, compromise data integrity, and disrupt operations, emphasizing the necessity of robust cybersecurity measures.
Insider Threats
Internal actors, including employees and contractors, pose a significant risk to data security. Whether through negligence or malicious intent, insiders with access to sensitive information can compromise data confidentiality and integrity. Implementing stringent access controls and monitoring mechanisms is imperative in mitigating insider threats.
Risks Associated with PII Exposure
The exposure of Personally Identifiable Information (PII) amplifies data security risks. PII, encompassing data like social security numbers and financial records, is a prime target for cybercriminals seeking to engage in identity theft and fraud. Organizations must prioritize data encryption, robust authentication protocols, and comprehensive employee training to mitigate the adverse impacts of PII exposure.
Emerging Threat Landscape
In addition to established threats, emerging technologies like the Internet of Things (IoT) and artificial intelligence introduce new vulnerabilities to data security. The interconnected nature of IoT devices and the vast amounts of data processed by AI systems present novel challenges for safeguarding sensitive information.
Importance of Regular Security Audits
Conducting regular security audits is essential for identifying vulnerabilities and ensuring compliance with data protection regulations. By performing comprehensive assessments of security protocols, organizations can proactively detect weaknesses and implement necessary enhancements to fortify their defenses.
Data Encryption Best Practices
Employing robust encryption protocols is fundamental in safeguarding data both at rest and in transit. Implementing industry-standard encryption algorithms and key management practices ensures that sensitive information remains secure even if unauthorized parties gain access to it.
Employee Training and Awareness
Educating employees about cybersecurity best practices and the importance of data security is critical in establishing a culture of vigilance within an organization. Regular training sessions, simulated phishing exercises, and awareness campaigns can empower staff to recognize and respond effectively to potential security threats.
Conclusion
As the digital landscape evolves, the importance of data security cannot be overstated. By staying informed about prevalent threats, adopting proactive security measures, and fostering a culture of cybersecurity awareness, individuals and organizations can fortify their defenses against data breaches and cyber threats.
Understanding PII Masking
Defining PII Masking and Its Role in Data Protection
The protection of sensitive data is of utmost importance. Personally Identifiable Information (PII) refers to any data that can be used to identify a particular individual. This includes information such as names, social security numbers, addresses, phone numbers, email addresses, and more. PII masking is a crucial technique used to safeguard this information.
PII masking involves concealing or encrypting sensitive data to prevent unauthorized access. By replacing or hiding certain characters within the data, the original information is obscured, making it unreadable to anyone without proper authorization. This process helps mitigate the risks associated with data breaches and unauthorized disclosure.
Exploring the Importance of PII Masking Strategies
Implementing effective PII masking strategies is essential for organizations that handle sensitive data. By employing robust masking techniques, companies can reduce the likelihood of data exposure and protect the privacy of their customers. Some common PII masking methods include:.
- Randomization : Replacing actual data with random values to maintain data integrity while ensuring privacy.
- Substitution : Masking original values with fictitious but structurally similar data to preserve the format.
- Shuffling : Rearranging the order of characters within PII fields to obfuscate the information.
- Tokenization : Generating unique tokens to represent PII, allowing secure storage and transmission of data without revealing sensitive details.
By incorporating these strategies into their data protection protocols, organizations can enhance security measures and comply with privacy regulations such as GDPR and CCPA.
Advanced PII Masking Techniques
As data protection requirements evolve, advanced PII masking techniques have emerged to address new challenges. One such technique is Format-Preserving Encryption (FPE), which allows for the encryption of data while preserving its original format. This is particularly useful in situations where maintaining the structure of the data is crucial for processing and analysis.
Another innovative approach is Dynamic Data Masking (DDM), which dynamically masks sensitive data in real-time based on user roles and access privileges. DDM ensures that only authorized individuals can view the complete information, enhancing data security in multi-user environments.
Best Practices for Implementing PII Masking
To ensure the effectiveness of PII masking strategies, organizations should follow some best practices:.
- Conduct regular audits to identify any gaps in data protection measures and refine masking processes accordingly.
- Encrypt PII data at rest and in transit to prevent unauthorized access at all stages.
- Implement access controls and user authentication protocols to restrict data access based on user roles and responsibilities.
- Provide training to employees on the importance of data security and the proper handling of sensitive information.
By adopting these best practices, organizations can strengthen their data protection frameworks and uphold the trust of their stakeholders.
Understanding PII masking and the evolving landscape of data protection is essential for organizations seeking to safeguard sensitive information and comply with regulatory requirements. By implementing robust masking techniques and staying informed about emerging trends, businesses can mitigate risks, protect privacy, and maintain data integrity in an increasingly digitized world.
Effective PII Masking Strategies
Anonymization and Pseudonymization Techniques
In the realm of data privacy and security, protecting Personally Identifiable Information (PII) is a top priority. One of the key strategies employed for this purpose is the use of anonymization and pseudonymization techniques. Anonymization involves removing any identifying information from datasets, making it impossible to link the data back to an individual. Pseudonymization, on the other hand, replaces identifiable data with artificial identifiers or pseudonyms, allowing data to be matched up without revealing the actual identities involved.
Tokenization Methods for Securing PII
Another effective PII masking approach is tokenization. This process involves replacing sensitive data with unique tokens that have no inherent meaning or value. The original data is securely stored in a separate location, while the tokenized data can be used for various operations without compromising the actual PII. Tokenization is widely used in payment processing systems and other scenarios where data security is paramount.
Data Encryption as a PII Masking Approach
Data encryption is a fundamental technique for securing PII. By converting data into a coded format that can only be accessed with the correct decryption key, encryption ensures that even if the data is intercepted, it remains unreadable and protected. End-to-end encryption, in particular, is essential for safeguarding PII during transit or storage, as it encrypts data from the point of origin to its final destination.
Data Masking Techniques
Apart from anonymization, pseudonymization, tokenization, and encryption, there are other effective data masking techniques that organizations can implement to protect PII. Some of these techniques include data shuffling, where the values in a dataset are randomly rearranged to break any direct link to the original data, and data substitution, which involves replacing sensitive information with fictitious but realistic data to maintain the structure of the dataset while protecting privacy.
Regulatory Compliance and PII Masking
Compliance with data protection regulations such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA) is vital for businesses handling PII. Implementing robust PII masking strategies not only helps in safeguarding sensitive information but also ensures legal compliance with these regulations. Organizations must stay updated with the evolving regulatory landscape to adapt their data masking techniques accordingly.
Best Practices for PII Masking
To enhance the effectiveness of PII masking strategies, organizations should adopt best practices such as implementing role-based access controls to restrict data access based on user roles, conducting regular audits to monitor data handling practices and identify vulnerabilities, and educating employees on the importance of data privacy and security. Additionally, employing a risk-based approach to data masking can help organizations prioritize their efforts based on the level of risk associated with different datasets containing PII.
Effective PII masking strategies are essential for safeguarding sensitive information and maintaining data privacy in an increasingly interconnected digital landscape. By combining anonymization, pseudonymization, tokenization, encryption, and other data masking techniques with regulatory compliance and best practices, organizations can establish a robust data protection framework that mitigates risks associated with PII exposure and ensures trust among stakeholders.
This blog section has discussed various PII masking strategies, emphasizing the importance of data privacy and security in today’s data-driven world. Implementing a comprehensive approach to PII masking not only protects sensitive information but also builds a foundation of trust with customers, partners, and regulatory bodies.
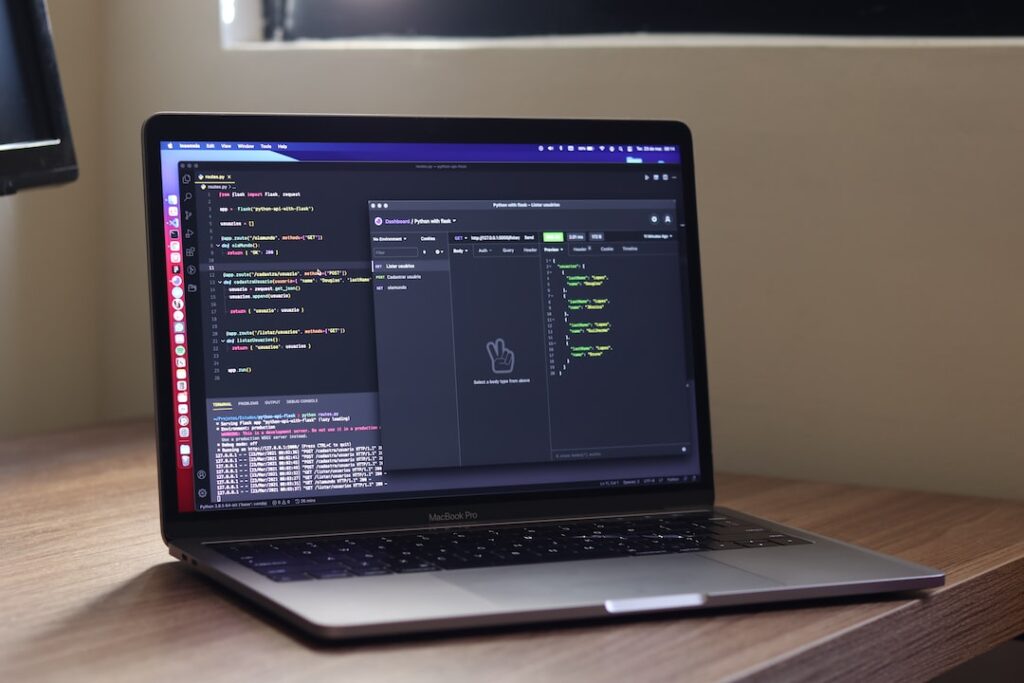
Implementing PII Masking in Practice
Steps to Successfully Integrate PII Masking into Data Handling Processes
Safeguarding Personally Identifiable Information (PII) is vital to maintaining data privacy and security. Implementing PII masking is a critical measure to protect sensitive information from unauthorized access. Let’s delve into the key steps required to seamlessly integrate PII masking into your data handling processes:.
-
Identifying PII Data: The initial phase involves identifying PII data elements present in your datasets. These may include social security numbers, credit card details, addresses, and other sensitive information that require protection.
-
Defining Masking Rules: Once PII data is identified, establish clear masking rules to determine how the information will be obscured. Common techniques for masking include data substitution, shuffling, and encryption to ensure the confidentiality of sensitive data.
-
Leveraging Data Masking Tools: Utilize advanced data masking tools and software to automate the masking process efficiently. These tools streamline the application of masking rules across various databases, reducing manual effort and enhancing data security.
-
Testing Masking Implementation: Before full deployment, rigorously test the PII masking implementation to validate its effectiveness. Verify that the masked data remains usable for legitimate purposes while effectively securing sensitive information.
Best Practices for Securely Maintaining Masked PII
Following the successful implementation of PII masking, adherence to best practices is crucial to uphold the security of masked PII. Here are additional recommendations to help you securely manage masked PII:.
-
Implement Robust Access Controls: Enforce stringent access controls to limit access to unmasked PII data. Implement role-based access permissions and robust authentication mechanisms to restrict unauthorized data access.
-
Data Encryption Measures: Consider encrypting both masked and unmasked PII data to enhance data security. Encryption adds an extra layer of protection, safeguarding data integrity both at rest and in transit.
-
Regular Security Audits: Conduct periodic security audits to monitor data handling processes and ensure compliance with data protection laws. Audits help identify potential vulnerabilities and gaps in the PII masking implementation, allowing for timely remediation.
-
Employee Training Programs: Provide comprehensive training to employees handling masked PII data. Educate staff on data security best practices, proper data handling procedures, and incident response protocols to mitigate data breaches.
By adhering to these comprehensive steps and best practices, organizations can effectively implement PII masking protocols in practice, fortifying the security of sensitive data assets.
Benefits of Effective PII Masking
Enhanced Data Privacy and Compliance with Regulations
Where personal data is constantly being collected and processed, ensuring enhanced data privacy is crucial. Implementing effective Personally Identifiable Information (PII) masking techniques can help organizations protect sensitive information from unauthorized access. By masking PII such as social security numbers, credit card details, and addresses, businesses can reduce the risk of data breaches and maintain compliance with data protection regulations like GDPR and HIPAA.
Mitigating the Risks of Data Breaches
Data breaches can have severe consequences for businesses, including financial losses, reputational damage, and legal implications. PII masking plays a vital role in mitigating these risks by obscuring sensitive information and making it unreadable to anyone without proper authorization. By implementing robust PII masking solutions, organizations can safeguard their data assets and prevent unauthorized access, ensuring the integrity and confidentiality of customer information.
Safeguarding Against Identity Theft
Identity theft is a growing concern in today’s interconnected world. Hackers and cybercriminals are constantly seeking to exploit vulnerabilities in data security to steal personal information for fraudulent purposes. Effective PII masking serves as a powerful deterrent against identity theft by rendering sensitive data unusable even if a breach occurs. This added layer of protection can help individuals and organizations alike avoid the devastating consequences of identity theft.
Maintaining Customer Trust and Loyalty
Customers today are more aware of data privacy issues and expect businesses to handle their personal information responsibly. By implementing robust PII masking measures, organizations demonstrate their commitment to protecting customer data and respecting privacy rights. This proactive approach not only helps in complying with regulations but also fosters trust and loyalty among customers. When individuals feel confident that their information is secure, they are more likely to engage with a business and maintain long-lasting relationships.
Enhancing Data Governance and Security
Effective PII masking is a fundamental aspect of comprehensive data governance and security strategies. By incorporating masking techniques into data handling processes, organizations establish a strong foundation for data protection and risk management. Properly masked PII reduces the likelihood of unauthorized access and minimizes the impact of potential security incidents. Furthermore, robust data governance practices enhance overall data quality, consistency, and integrity, enabling organizations to make informed decisions based on reliable information.
The benefits of effective PII masking extend far beyond simple data obfuscation. By prioritizing data privacy, mitigating data breach risks, safeguarding against identity theft, maintaining customer trust, and enhancing data governance, organizations can create a secure and compliant environment for their data assets. Embracing PII masking as a proactive security measure not only protects sensitive information but also strengthens relationships with customers and upholds the principles of privacy and trust in the digital landscape.
Conclusion
Implementing effective personally identifiable information (PII) masking strategies is essential in safeguarding sensitive data from unauthorized access. By utilizing techniques such as encryption, tokenization, and data anonymization, organizations can significantly reduce the risk of data breaches and protect the privacy of their customers. It is crucial for businesses to prioritize data security and compliance with regulations to build trust with their stakeholders and maintain a strong reputation in today’s digital landscape.