Safeguarding sensitive assets and information is a top priority for organizations. Utilizing a. Role-Based Access Control (RBAC) Permission framework is a strategic approach to managing and enforcing access controls effectively. With RBAC, user roles are assigned based on responsibilities and permissions, ensuring that only authorized individuals can access specific resources. This proactive method helps mitigate risks such as data breaches, insider threats, and unauthorized access attempts. RBAC streamlines security protocols, enhances regulatory compliance, and simplifies access management processes. Moreover, the scalability and ease of maintenance provided by RBAC frameworks empower organizations to adapt swiftly to evolving security challenges. By embracing RBAC strategies, businesses can fortify their security posture and protect critical assets in an ever-evolving threat landscape.
Key Concepts of RBAC
Definition and Purpose of RBAC
Role-Based Access Control (RBAC) is a method of restricting network access based on the roles of individual users within an organization. It ensures that only authorized users have access to certain information and resources, based on their roles in the company. The primary purpose of RBAC is to limit exposure to data breaches and ensure that sensitive information is only accessible to those who need it.
Benefits of RBAC in Security
- Granular Access Control : RBAC allows for precise control over who can access what information, reducing the risk of unauthorized access.
- Simplified Management : With RBAC, access rights are assigned based on job roles, making it easier to manage permissions across an organization.
- Improved Compliance : RBAC helps organizations meet regulatory compliance requirements by ensuring that access to sensitive data is restricted to authorized personnel only.
- Enhanced Security : By limiting access to sensitive information, RBAC strengthens the overall security posture and reduces the likelihood of data breaches.
- Scalability : RBAC is scalable and can adapt to organizational changes by easily assigning or revoking access based on role changes or employee turnover.
Comparison with Other Access Control Models
- DAC (Discretionary Access Control) : In DAC, users have control over their resources and can grant access to others. In contrast, RBAC is more structured and centrally managed.
- MAC (Mandatory Access Control) : MAC is based on security labels assigned to information and users. RBAC, on the other hand, focuses on roles and permissions based on job functions.
- ABAC (Attribute-Based Access Control) : ABAC considers attributes of users, resources, and the environment to make access control decisions. RBAC, however, is based on predefined roles and permissions.
- Role Hierarchies : RBAC can establish role hierarchies, allowing for inheritance of permissions within an organization’s structure, streamlining access management.
RBAC is an effective access control model that offers numerous benefits in terms of security, compliance, and management. Understanding the key concepts of RBAC is crucial for organizations looking to enhance their cybersecurity defenses. By implementing RBAC, organizations can not only improve their security posture but also streamline access management and ensure regulatory compliance, making it a vital component of a robust cybersecurity strategy.
Implementing RBAC for Enhanced Security
Steps to Successfully Deploy RBAC
Role-Based Access Control (RBAC) is a crucial security measure for organizations. Implementing RBAC requires careful planning and execution to ensure maximum effectiveness. Here are the steps to successfully deploy RBAC:.
-
Identify Roles : Begin by identifying all possible roles within the organization based on job functions, responsibilities, and required access levels.
-
Define Role Permissions : Once roles are identified, define the specific permissions and access levels each role should have. This step is essential for ensuring that users have the appropriate level of access.
-
Assign Users to Roles : After defining roles and permissions, assign users to the corresponding roles based on their job responsibilities and the principle of least privilege.
-
Role Mapping : Map roles to specific resources or data within the organization to streamline access management and ensure data security.
-
Continuous Monitoring and Updates : Regularly monitor and update role assignments to adapt to organizational changes and maintain security compliance.
Role Hierarchy and Permission Assignment
In addition to the basic steps, implementing a clear role hierarchy and permission assignment strategy is crucial:.
-
Role Hierarchy : Establish a clear hierarchy of roles where higher-level roles inherit permissions from lower-level roles. This hierarchy simplifies access control and ensures consistency.
-
Permission Assignment : Assign permissions at the appropriate level in the role hierarchy to prevent unauthorized access while enabling users to fulfill their job duties effectively.
Case Studies on RBAC Implementation
Examining real-world case studies can provide valuable insights into the practical benefits of RBAC:.
-
Company X : By implementing RBAC, Company X significantly enhanced security measures for sensitive financial data. Roles like ‘Finance Manager’ and ‘Accountant’ were created with specific permissions, improving data protection.
-
Healthcare Institution Y : RBAC helped Healthcare Institution Y secure patient records by creating roles such as ‘Doctor’ and ‘Nurse’ with tailored permissions, ensuring patient data confidentiality.
-
Tech Company Z : Tech Company Z leveraged RBAC to safeguard internal systems. Roles like ‘System Administrator’ and ‘Developer’ were granted appropriate permissions, minimizing unauthorized access risks.
The successful implementation of RBAC is essential for bolstering organizational security. By following the outlined steps, establishing role hierarchies, and drawing insights from case studies, businesses can fortify their access control mechanisms and data security practices.
Advantages and Challenges of Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is a widely adopted approach in security management due to its myriad advantages and challenges. Let’s delve deeper into the benefits and hurdles associated with RBAC.
Advantages of RBAC in Security Management
RBAC offers a structured method for managing user permissions by assigning roles based on their responsibilities within an organization. The advantages of RBAC are multifaceted:.
-
Enhanced Security: RBAC boosts security by limiting user access to only the resources essential for their roles, thereby minimizing the risk of unauthorized access.
-
Streamlined Administration: RBAC streamlines user access management by consolidating permissions according to roles, facilitating the assignment and revocation of access rights.
-
Scalability: RBAC enables organizations to efficiently scale their access control systems as their user and resource base expands, all while upholding security standards.
Addressing Challenges in RBAC Adoption
Despite its benefits, RBAC implementation can present challenges:.
-
Role Proliferation: Organizations may face an escalation in the number of roles as they grow, leading to role proliferation and complicating effective role management.
-
Role Allocation: Determining suitable roles for users can be intricate, particularly in large organizations with diverse job roles and responsibilities.
-
Precise Role Permission Assignment: Accurately mapping permissions to roles, without over or under-permissioning users, demands meticulous planning and continuous oversight.
Real-world Examples of RBAC Success Stories
Numerous organizations have successfully harnessed RBAC, witnessing tangible improvements in security and access control:.
-
Tech Giant Success Story: A tech giant implemented RBAC to streamline access control and fortify data security across its global operations, resulting in enhanced efficiency and reduced security risks.
-
Financial Services Firm Case Study: A financial services firm leveraged RBAC to bolster regulatory compliance and mitigate data breach risks by enforcing granular access controls.
-
Healthcare Institution Example: A healthcare institution utilized RBAC to safeguard patient data confidentiality and enforce stringent access protocols for medical personnel, ensuring compliance with privacy regulations.
Challenges in RBAC Implementation
While RBAC offers significant benefits, organizations may encounter hurdles during implementation:.
-
Integration Complexity: Integrating RBAC into existing systems can be complex, requiring thorough analysis and potential system modifications.
-
User Resistance: Some users may resist RBAC changes due to unfamiliarity or perceived limitations in their access capabilities.
-
Maintenance Overhead: Regular maintenance and periodic review of roles and permissions are necessary to ensure RBAC remains effective and aligned with organizational changes.
Future Trends in RBAC
Looking ahead, RBAC is expected to evolve to meet the demands of modern security landscapes. Future trends may include:.
-
Automation: Increased automation in role assignment and permission management to enhance efficiency and reduce manual errors.
-
Adaptive Access Control: Implementing adaptive access control mechanisms that dynamically adjust permissions based on user behavior and context.
-
Integration with AI: Leveraging artificial intelligence to optimize role assignments, identify anomalies, and improve overall security posture.
Role-Based Access Control brings substantial benefits to security management but requires careful planning and ongoing maintenance to overcome challenges and maximize its effectiveness in safeguarding organizational resources and data.
Future Trends and Innovations in RBAC
Role-Based Access Control (RBAC) has been a cornerstone in modern security practices, gradually evolving to meet the dynamic needs of organizations in safeguarding their digital assets. This blog section delves into the future trends and innovations shaping RBAC, highlighting the critical role it plays in ensuring robust security measures.
Evolution of RBAC in Modern Security Practices
RBAC has come a long way from its inception, adapting to the increasingly complex security landscape. Initially designed to manage access based on user roles, RBAC now incorporates advanced features like attribute-based access control and dynamic authorization. These enhancements allow organizations to fine-tune access permissions based on contextual information, enhancing security and compliance.
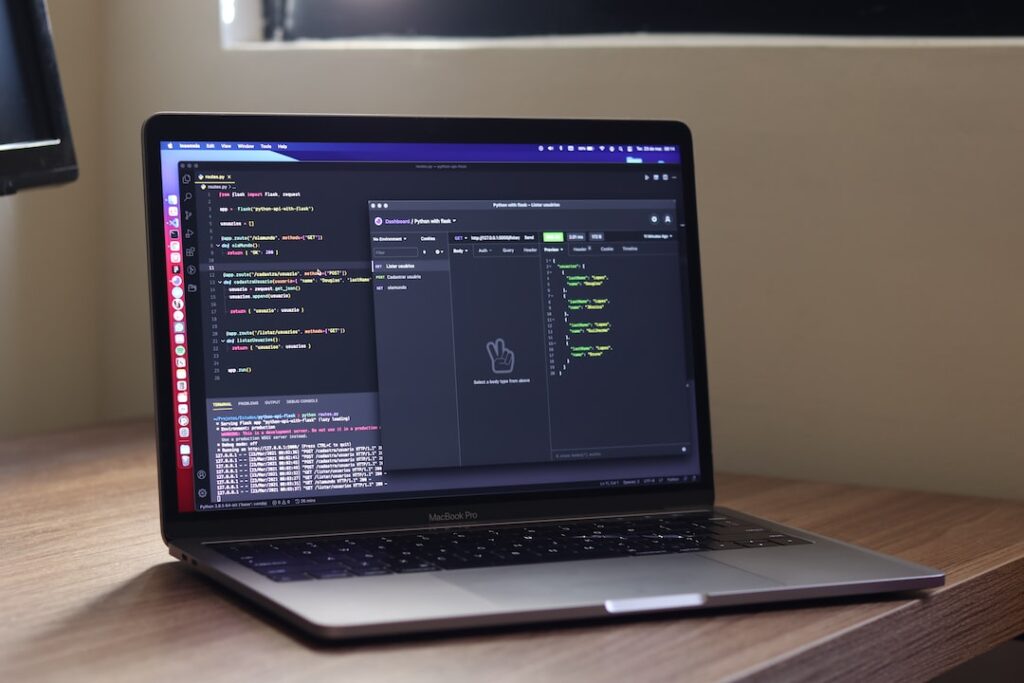
Role of RBAC in Cloud Security
In the realm of cloud security, RBAC serves as a fundamental mechanism for controlling access to cloud resources. As cloud environments become more intricate, RBAC helps organizations maintain granular control over user privileges, reducing the risk of data breaches and unauthorized access. Additionally, RBAC facilitates the implementation of the principle of least privilege, ensuring that users only have access to the resources necessary for their roles, thereby reducing the attack surface.
Incorporating AI and ML in RBAC Systems
The fusion of Artificial Intelligence (AI) and Machine Learning (ML) with RBAC heralds a new era of adaptive access control. By harnessing AI algorithms for user behavior analysis and ML models for anomaly detection, RBAC systems can proactively identify and respond to security threats in real-time. Moreover, AI-driven RBAC solutions offer predictive access control, dynamically adjusting permissions based on user activity patterns and risk scores.
Enhancing RBAC with Blockchain Technology
Integrating blockchain technology with RBAC systems introduces a new level of security and transparency. By leveraging blockchain’s decentralized and immutable nature, RBAC implementations can enhance auditability, ensuring that access control decisions are tamper-proof and traceable. This fusion not only strengthens security but also simplifies compliance efforts by providing a verifiable record of access control actions.
The Rise of Zero Trust RBAC
In the era of zero trust security models, RBAC is evolving to align with the principles of least privilege and continuous authentication. Zero trust RBAC emphasizes the verification of every access attempt, regardless of the user’s location or network environment. This approach minimizes the risk of insider threats and lateral movement within networks, bolstering overall security posture.
As organizations embrace digital transformation and confront evolving cybersecurity challenges, the synergy between RBAC, AI, ML, blockchain, and zero trust principles will play a pivotal role in fortifying defense mechanisms and ensuring data integrity. Stay tuned as we delve deeper into these innovative trends and their implications for the future of RBAC and cybersecurity.
Conclusion
Implementing Role-Based Access Control (RBAC) permission frameworks is a crucial step in enhancing security measures within organizations. By assigning specific roles and permissions to users based on their responsibilities and job functions, RBAC helps prevent unauthorized access to sensitive data and systems. This proactive approach not only strengthens security but also streamlines access management processes, ensuring compliance with regulatory requirements. Overall, embracing RBAC permission frameworks is a strategic investment towards safeguarding valuable assets and maintaining a secure environment in today’s digital landscape.