Businesses heavily rely on APIs to facilitate seamless communication between various systems and platforms. However, this increased connectivity also brings forth a higher susceptibility to security breaches and vulnerabilities. Constant surveillance through API monitoring is essential to detect and thwart potential security threats in real-time. By scrutinizing API traffic, endpoint activities, and access permissions, organizations can proactively identify and address security weaknesses before they are exploited by malicious entities. This proactive approach not only safeguards sensitive data and intellectual property but also ensures the smooth operation of vital business functions. Recognizing the significance of robust API monitoring is imperative for companies looking to fortify their cybersecurity defenses and uphold a safe work atmosphere.
Benefits of API Monitoring for Workplace Security
Real-time Threat Detection
API monitoring provides real-time insights into potential security threats by monitoring API traffic for any unusual behavior or unauthorized access attempts. This allows organizations to proactively identify and address security vulnerabilities before they escalate into major incidents. Real-time threat detection is crucial in today’s dynamic cybersecurity landscape where threats evolve rapidly, and organizations need to stay ahead of potential risks.
Data Protection and Privacy Compliance
By monitoring API interactions, organizations can ensure that sensitive data is being handled securely and in compliance with data protection regulations. API monitoring helps in detecting any unauthorized access to sensitive information and ensures that data privacy requirements are met. Ensuring data protection and privacy compliance is not only essential for maintaining trust with customers and partners but also for avoiding regulatory penalties and reputational damage.
Policy Enforcement
API monitoring enables organizations to enforce security policies related to data access, authentication, and authorization. By monitoring API traffic, organizations can ensure that only authorized users and applications are accessing the data, thereby reducing the risk of data breaches and ensuring workplace security. Policy enforcement through API monitoring is critical for maintaining the integrity of data access controls and preventing unauthorized data leaks.
Improved Incident Response
In addition to proactive threat detection, API monitoring plays a vital role in incident response. By continuously monitoring API traffic, organizations can quickly detect and respond to security incidents, minimizing the impact of breaches and reducing downtime. Improved incident response capabilities are essential for mitigating the consequences of security breaches and ensuring business continuity.
Enhanced Performance Optimization
API monitoring not only contributes to security but also helps in optimizing system performance. By analyzing API performance metrics and identifying bottlenecks or inefficiencies, organizations can fine-tune their systems for better responsiveness and scalability. Enhanced performance optimization through API monitoring leads to improved user experience, increased productivity, and cost savings for the organization.
Compliance Auditing and Reporting
Maintaining compliance with industry regulations and internal policies is a continuous process. API monitoring facilitates compliance auditing by providing detailed logs and reports on API activities. These audit trails not only aid in regulatory compliance assessments but also serve as valuable insights for improving security practices and optimizing operational processes.
API monitoring is a cornerstone of workplace security, offering a comprehensive approach to threat detection, data protection, policy enforcement, incident response, performance optimization, and compliance auditing. By leveraging API monitoring tools and practices, organizations can safeguard their data, uphold privacy standards, and fortify their security posture in an ever-evolving digital environment.
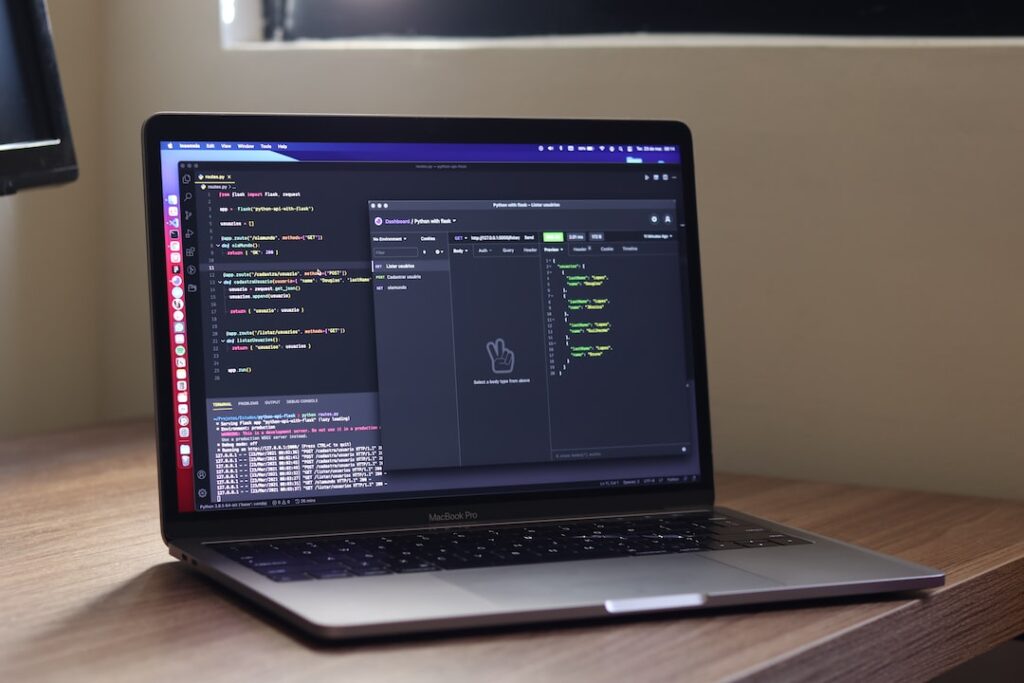
Best Practices for Implementing API Monitoring
When it comes to ensuring the security, performance, and compliance of APIs, implementing best practices in API monitoring is crucial. Continuous monitoring serves as a foundation for detecting issues promptly and maintaining service reliability. Integration with robust security systems is vital for protecting sensitive data and preventing unauthorized access.
In the realm of API management, defining clear specifications and leveraging API gateways for efficient routing are foundational steps. Robust authentication and authorization mechanisms provide an additional layer of security, effectively mitigating potential threats.
Within the developer portal setup, offering comprehensive API documentation and interactive consoles significantly enhances the developer experience, encouraging API reuse and unlocking monetization opportunities. Enforcing governance policies and standards guarantees consistency and compliance throughout all API implementations.
Analytics and performance monitoring play pivotal roles in effective API monitoring. Monitoring key metrics like API calls, response times, and error rates offer valuable insights into system performance and user experience. Regular auditing and reporting are essential for identifying issues, ensuring data protection, and complying with industry standards.
Security testing is a critical aspect of API monitoring. Regular security assessments help proactively identify and mitigate vulnerabilities and threats.
To further enhance API monitoring and security practices, organizations should adopt a security-first approach, leverage pre-built integration code, and integrate continuous deployment pipelines. These strategies streamline monitoring processes, enhance security posture, and lead to more efficient API implementations.
Additionally, providing incentives for API reuse, enforcing strict governance policies, and monitoring key performance indicators like scalability and reliability contribute to a robust API monitoring framework. Keeping security protocols updated, staying informed about emerging threats, and fostering a security-conscious culture among developers and stakeholders are crucial for maintaining a secure API environment.
By incorporating these best practices, organizations can establish a proactive and comprehensive approach to API monitoring, ensuring the integrity and reliability of their API ecosystem while effectively mitigating potential risks.
Challenges in API Monitoring and Workplace Security
The reliance on APIs (Application Programming Interfaces) for various functionalities has become ubiquitous, presenting a myriad of challenges in terms of monitoring and workplace security. This blog section will delve into the complexities faced in API monitoring and the critical importance of workplace security in ensuring data integrity while balancing security and usability.
Complexity of Modern APIs
The rapid expansion of APIs in modern software architecture has ushered in a new era of complexity in monitoring practices. Organizations are grappling with the sheer volume and diversity of APIs utilized, making it increasingly challenging to effectively track and manage them. This complexity not only hinders the identification of performance issues, security vulnerabilities, and compliance risks but also necessitates advanced monitoring tools and strategies to ensure comprehensive oversight.
Ensuring Data Integrity
At the heart of API monitoring and workplace security lies the fundamental principle of data integrity. The seamless transmission of accurate and consistent data through APIs is paramount in upholding user trust and safeguarding sensitive information. Any breach in data integrity can lead to severe repercussions, such as financial ramifications and irreparable damage to an organization’s reputation. Implementing robust data validation processes and encryption techniques is essential in mitigating risks associated with data integrity compromises.
Balancing Security and Usability
A delicate equilibrium must be struck between stringent security measures and user-friendly interfaces in the realm of API monitoring and workplace security. While robust security protocols are imperative for shielding against cyber threats, overly restrictive measures can impede operational efficiency and hinder user experience. Organizations must adopt a holistic approach that integrates user-centric design with robust security frameworks to facilitate seamless data exchange without compromising on data security.
Emerging Trends in API Monitoring
As technology evolves, new trends in API monitoring are emerging to address the evolving threat landscape. Concepts such as AI-driven anomaly detection, behavior analytics, and real-time monitoring are gaining prominence in enhancing the security posture of API ecosystems. By leveraging these innovative approaches, organizations can proactively detect and respond to potential security incidents, ensuring the continuous protection of sensitive data.
Regulatory Compliance and Workplace Security
In addition to technological advancements, regulatory compliance plays a pivotal role in shaping workplace security practices. Adhering to data protection regulations such as GDPR, HIPAA, or PCI DSS is crucial for maintaining the legal and ethical standards of data handling. Organizations must stay abreast of evolving compliance requirements and implement robust security measures to safeguard against non-compliance penalties and data breaches.
Conclusion
The evolving landscape of API monitoring and workplace security necessitates proactive measures and adaptive strategies to combat emerging threats effectively. By prioritizing continuous monitoring, fostering a culture of cybersecurity awareness, and leveraging cutting-edge technologies, organizations can fortify their defenses and cultivate a secure and productive work environment. Stay tuned for more insights on navigating the complexities of API monitoring and workplace security in our future blog posts.
Section: Case Studies: Successful Implementation of API Monitoring
API monitoring has become a cornerstone of modern cybersecurity strategies, with companies across industries recognizing its pivotal role in safeguarding digital assets and ensuring regulatory compliance. Let’s delve deeper into some compelling case studies that highlight the successful implementation of API monitoring:.
Company A: Enhancing Security Measures
Company A, a leading tech company, implemented API monitoring to fortify its security measures. By vigilantly monitoring all incoming and outgoing API calls, Company A not only detected and prevented security threats in real-time but also established a robust security foundation. Through the deployment of cutting-edge threat detection algorithms and regular security audits, Company A significantly lowered its susceptibility to cyber attacks, showcasing the effectiveness of proactive security measures.
Company B: Mitigating Data Breaches
The financial sector witnessed how Company B leveraged API monitoring to mitigate data breaches effectively. By continuously monitoring API activities and configuring alerts for unusual patterns, Company B swiftly identified and remedied security incidents. This proactive stance not only shielded customer data but also bolstered the organization’s overall cybersecurity posture. Moreover, the integration of machine learning algorithms empowered Company B to predict security breaches and preemptively address vulnerabilities, demonstrating the power of predictive analytics in cybersecurity.
Company C: Achieving Regulatory Compliance
In a heavily regulated industry like healthcare, Company C utilized API monitoring to attain regulatory compliance seamlessly. By scrutinizing data exchanges through APIs, Company C ensured adherence to stringent regulatory mandates. This proactive approach not only facilitated compliance with industry standards but also fostered trust among patients and regulatory bodies. Additionally, Company C implemented stringent access controls and robust data encryption protocols to uphold data integrity and confidentiality, aligning with the stringent data protection regulations prevalent in the healthcare sector.
These case studies underscore the indispensable nature of successful API monitoring implementations in fortifying security measures, thwarting data breaches, and navigating regulatory frameworks. By embracing a proactive and sophisticated approach to API monitoring, organizations can shield their digital ecosystems, cultivate customer trust, and surmount regulatory hurdles in the ever-evolving cybersecurity landscape.
Conclusion
API monitoring plays a crucial role in ensuring workplace security by providing real-time visibility into data exchanges, detecting potential threats, and preventing unauthorized access. By implementing robust API monitoring strategies, organizations can effectively safeguard their systems, protect sensitive information, and mitigate security risks, ultimately fostering a secure work environment for employees and stakeholders alike. It is imperative for businesses to prioritize API monitoring as part of their overall security measures to stay ahead of evolving cybersecurity threats and maintain the integrity of their operations.