In the rapidly changing realm of technology and data-driven business practices, maintaining effective governance is crucial for ensuring security, compliance, and operational efficiency. Role-Based Access Control (RBAC) permission frameworks serve as a cornerstone in upholding order and oversight within APIs and integrations. By aligning permissions with predefined roles, RBAC empowers organizations to efficiently manage access privileges, mitigating the risks associated with unauthorized entry and potential security lapses. This methodology not only bolsters security protocols but also simplifies the process of assigning and withdrawing permissions, ultimately enhancing overall governance and adherence to regulatory standards. As we navigate the digital landscape where data protection and compliance are paramount concerns, grasping the significance of RBAC in API and integration governance emerges as a critical element for enterprises seeking to protect their assets and fortify operational resilience.
Understanding RBAC Permission Frameworks
RBAC, which stands for Role-Based Access Control, is a permission framework that regulates access to computer resources based on the roles of individual users within an organization. In this system, permissions are associated with roles, and users are assigned to appropriate roles, which in turn grant access to specific resources and functionality. This approach simplifies the management of permissions and ensures that users have the necessary access rights to perform their tasks effectively.
How RBAC Works
RBAC operates on the principle of least privilege, where users are only granted the permissions they need to fulfill their job responsibilities. The core elements of RBAC include roles, permissions, and access control. Roles define the responsibilities and access levels within an organization, permissions specify what actions users can perform, and access control enforces these permissions by restricting unauthorized access.
Benefits of RBAC in Governance
Implementing RBAC offers several benefits, especially in terms of governance and security. By aligning access privileges with job roles, RBAC helps organizations maintain compliance with regulations and internal policies. It also simplifies auditing processes by providing a clear overview of who has access to what resources. Additionally, RBAC enhances security by reducing the risk of unauthorized access and limiting the potential impact of security breaches, ultimately contributing to a more robust cybersecurity posture.
Enhanced Security Measures in RBAC
One of the primary advantages of RBAC is its ability to enhance security measures within an organization. By implementing RBAC, companies can significantly reduce the risk of internal threats and unauthorized access. The principle of least privilege ensures that users are only granted access to the resources essential for their designated roles, minimizing the attack surface and potential damage from security breaches.
Scalability and Flexibility
RBAC frameworks offer scalability and flexibility, making them suitable for organizations of varying sizes and structures. As businesses grow and evolve, RBAC systems can adapt to accommodate changing roles and responsibilities. This scalability ensures that access control remains effective even as the organization undergoes expansion or restructuring.
Compliance and Auditing
RBAC plays a crucial role in ensuring compliance with regulatory requirements and facilitating auditing processes. By aligning access rights with specific job functions, organizations can easily demonstrate adherence to industry regulations and internal policies. Auditors can quickly verify that access controls are appropriately configured and that users only have permissions necessary for their roles, streamlining compliance assessments and regulatory audits.
Conclusion
A thorough understanding of RBAC permission frameworks is essential for organizations seeking to enhance security, streamline access management, and maintain compliance with regulatory standards. By implementing RBAC systems, businesses can establish robust security measures, achieve operational efficiency, and mitigate the risks associated with unauthorized access. Embracing RBAC not only strengthens an organization’s cybersecurity posture but also contributes to overall governance and risk management strategies, positioning the company for long-term success in an increasingly digital landscape.
Implementing RBAC in API and Integration Governance
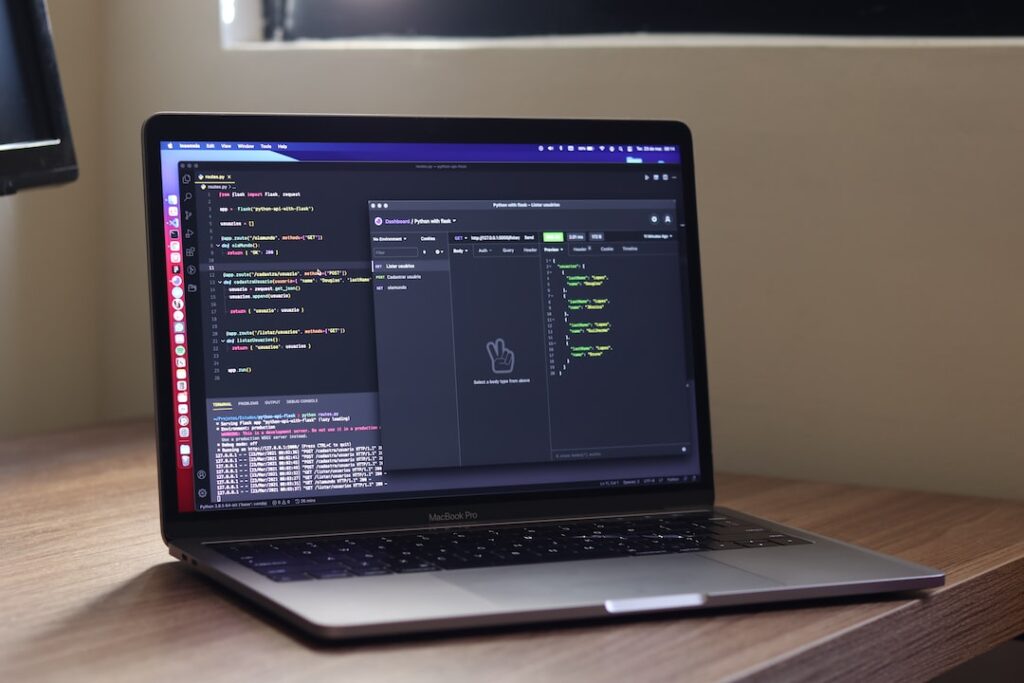
Integration of RBAC in API Security
Role-Based Access Control (RBAC) plays a critical role in ensuring the security of APIs by allowing organizations to control access to resources based on roles and permissions. By integrating RBAC into API security measures, organizations can enforce fine-grained access controls, reducing the risk of unauthorized access and potential data breaches. Implementing RBAC involves defining roles, assigning permissions, and managing user access based on their roles within the organization.
Best Practices for RBAC Implementation
-
Role Mapping: Establish clear role definitions and responsibilities to facilitate the effective implementation of RBAC. Clearly defining roles helps in determining the appropriate level of access for each user.
-
Least Privilege Principle: Adhering to the principle of least privilege ensures that users are granted only the minimum level of access required to perform their tasks. This practice helps reduce the attack surface and mitigates the risk of unauthorized access.
-
Regular Auditing: Regularly auditing roles and permissions is essential to ensure that access controls are correctly configured and aligned with the organization’s security policies. Periodic audits help identify and rectify any discrepancies or security loopholes.
-
Centralized Management: Utilizing centralized RBAC management tools streamlines the administration of roles and permissions across the organization. Centralized management enhances efficiency, simplifies role assignment, and ensures consistency in access control policies.
-
Role Inheritance: Implementing role inheritance simplifies the assignment and management of roles by allowing users to inherit permissions from higher-level roles. This practice reduces the complexity of managing individual user permissions.
Challenges and Solutions
Challenges:
-
Complexity: Implementing RBAC in API and integration governance can be challenging, particularly in complex organizational structures with diverse systems. Overcoming this complexity requires a comprehensive understanding of the organization’s structure and access requirements.
-
Scalability: Ensuring the scalability of RBAC as the organization grows and the number of users and resources increases is a common challenge. Scalability issues can be addressed by implementing flexible RBAC policies and scalable management solutions.
-
Integration: Integrating RBAC with existing systems and APIs without disrupting operations poses a significant challenge. Seamless integration requires careful planning, testing, and coordination to ensure a smooth transition.
-
User Experience: Balancing stringent security requirements with a user-friendly experience is crucial. Organizations must design RBAC systems that prioritize security without compromising usability and productivity.
Solutions:
-
Robust Planning: Conducting a thorough assessment of organizational needs and system requirements is essential before implementing RBAC. Robust planning helps identify potential challenges and design effective solutions.
-
Automation: Leveraging automation tools can streamline RBAC implementation and management processes, reducing manual efforts and ensuring consistency in access control policies.
-
Training and Awareness: Providing training to employees on RBAC concepts and best practices fosters a culture of security awareness and ensures smooth adoption of access control measures.
-
Continuous Monitoring: Implementing continuous monitoring and feedback mechanisms enables organizations to proactively identify and address security issues. Regular monitoring helps detect anomalies and unauthorized access attempts promptly.
By addressing these challenges and implementing best practices, organizations can successfully enhance their security posture and ensure regulatory compliance through the effective implementation of RBAC in API and integration governance.
Blog Section:
Case Studies: Successful Implementation of RBAC
Real-world Examples:
- XYZ Corporation’s RBAC Implementation Success Story
- ABC Company’s RBAC Best Practices
- DEF Enterprises: A Case Study in RBAC Efficiency
Lessons Learned:
- Key Takeaways from Implementing RBAC
- Common Challenges and How to Overcome Them
- Strategies for Seamless RBAC Integration
Impact on Governance:
- Enhancing Security Measures through RBAC
- RBAC’s Role in Regulatory Compliance
- RBAC as a Foundation for Strong Governance Frameworks
In this blog section, we will delve into the realm of Role-Based Access Control (RBAC) by exploring compelling case studies that showcase successful implementations of this access control model. Through an examination of real-world examples such as the acclaimed RBAC success story at XYZ Corporation, the best practices in RBAC adopted by ABC Company, and the remarkable efficiency achieved by DEF Enterprises through RBAC integration, readers will gain valuable insights into the diverse applications and benefits of RBAC across various industries and organizational structures.
Lessons Learned from these case studies will be dissected, offering readers key takeaways from successful RBAC implementations, strategies to address common challenges encountered during RBAC deployment, and recommendations for ensuring a seamless integration of RBAC within existing systems and processes.
Furthermore, we will analyze the profound Impact on Governance that RBAC brings, elucidating how RBAC enhances security measures by providing granular access controls, its pivotal role in ensuring regulatory compliance by aligning access privileges with industry standards, and how it serves as a foundational element for building robust governance frameworks that promote accountability and transparency within an organization.
By delving deeper into these case studies and their implications, readers will develop a comprehensive understanding of how RBAC transcends traditional access control mechanisms, offering a sophisticated approach to managing user permissions and access rights. Stay engaged as we unravel the transformative potential of RBAC in modern security architectures and governance strategies, shedding light on how this access control model can revolutionize organizational security practices and drive sustainable governance frameworks that adapt to evolving threat landscapes and compliance requirements.
Future of RBAC in API and Integration Governance
In the dynamic landscape of API and integration governance, Role-Based Access Control (RBAC) plays a crucial role in ensuring security, compliance, and efficiency. As technology continues to evolve, it is important to understand the future trends and predictions for RBAC and its significance in safeguarding data. Let’s delve into the future of RBAC and its impact on API and integration governance.
Emerging Trends
-
Zero Trust Architecture: With the increasing number of cyber threats, the adoption of Zero Trust Architecture is becoming essential. RBAC will continue to be a key component in implementing and enforcing Zero Trust principles to verify every user and device trying to access the network.
-
Automation and Orchestration: As organizations strive for agility and scalability, automation and orchestration of RBAC policies will be on the rise. The future of RBAC lies in its ability to adapt and scale according to dynamic business needs, which can be efficiently achieved through automation.
Predictions for RBAC Evolution
-
Context-Aware Access Control: RBAC will evolve to incorporate contextual factors such as location, time, and device posture to make access decisions. This evolution will enhance security by providing fine-grained access control based on real-time conditions.
-
Integration with AI and Machine Learning: The integration of RBAC with AI and machine learning algorithms will enable predictive access control decisions. By analyzing user behavior patterns and identifying anomalies, RBAC systems will proactively prevent unauthorized access.
Role in Ensuring Data Security
-
RBAC as a Compliance Enabler: RBAC frameworks will become indispensable in meeting regulatory compliance requirements such as GDPR and HIPAA. By defining roles, permissions, and access levels, organizations can ensure data security and privacy in accordance with industry standards.
-
Data Loss Prevention: RBAC will continue to play a vital role in data loss prevention strategies. By enforcing least privilege access and segregation of duties, RBAC minimizes the risk of data breaches and unauthorized data exposure.
The future of RBAC in API and integration governance looks promising with advancements in technology and security practices. By embracing emerging trends, predicting the evolution of RBAC, and recognizing its role in ensuring data security, organizations can effectively leverage RBAC to safeguard their digital assets and maintain a robust governance framework.
Conclusion
RBAC (Role-Based Access Control) permission frameworks are crucial for maintaining security and governance in API and integration environments. By implementing RBAC, organizations can effectively manage access control, reduce the risk of data breaches, and ensure compliance with regulations. The flexibility and granularity of RBAC empower organizations to assign permissions based on roles, making it easier to enforce security policies and protect sensitive information. As technology continues to evolve, the importance of RBAC in API and integration governance cannot be overstated, making it an essential tool for organizations striving to secure their systems and data.