In the realm of cybersecurity and access control, the implementation of Role-Based Access Control (RBAC) is pivotal for maintaining secure systems. However, the complexity arises when managing permission inheritance models within RBAC frameworks. To address this challenge, the concept of streamlining RBAC permission inheritance models emerges as a crucial focus area. By optimizing the way permissions are inherited and cascaded through roles, organizations can enhance security, reduce administrative overhead, and ensure granular access control. This introduction sets the stage for exploring the significance of refining RBAC permission inheritance models to bolster secure access management practices.
Understanding RBAC
Definition of Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is a method of restricting network access based on the roles of individual users within an organization. It is a widely used approach in cybersecurity to manage user permissions effectively. RBAC ensures that only authorized users are able to access certain resources and perform specific actions, reducing the risk of unauthorized access and data breaches.
Role Assignment, Permissions, and Enforcement
In RBAC, roles are created for various job functions within an organization. Permissions are then assigned to these roles to determine what actions users associated with the roles can perform. Additionally, RBAC includes enforcement mechanisms to ensure that access rights are consistently applied and enforced across the organization’s systems and applications.
Types of RBAC Models
-
Hierarchical RBAC : In this model, roles are organized in a hierarchical structure, where users inherit permissions from roles above them in the hierarchy. This simplifies the management of permissions by establishing clear relationships between different roles.
-
Static RBAC : Static RBAC involves the assignment of roles to users based on their job functions. These roles typically remain fixed and do not change frequently, providing stability in access control.
-
Dynamic RBAC : Dynamic RBAC offers more flexibility by allowing the creation of roles based on specific tasks or projects. Roles can be assigned and revoked as needed, adapting to changing organizational requirements and ensuring efficient access management.
Benefits of RBAC
- Enhanced Security : RBAC reduces the risk of unauthorized access and data breaches by ensuring that users only have access to the resources necessary for their roles.
- Simplified Access Management : By grouping permissions into roles, RBAC simplifies the process of managing user access rights and permissions.
- Scalability : RBAC can scale with the organization’s growth and evolving access control needs, providing a flexible framework for access management.
Implementing RBAC in Organizations
Implementing RBAC involves several key steps:.
-
Role Identification : Identify the different job functions and responsibilities within the organization to create appropriate roles.
-
Permission Assignment : Define the specific permissions associated with each role, ensuring that they align with the responsibilities of the role.
-
Role Mapping : Map roles to individual users or groups based on their job functions and access requirements.
-
Regular Review : Regularly review and update roles and permissions to adapt to organizational changes and ensure compliance.
Challenges of RBAC
While RBAC offers numerous benefits, organizations may face challenges such as:.
-
Role Proliferation : As organizations grow, the number of roles can increase, making role management complex.
-
Role Inheritance Complexity : In hierarchical RBAC models, managing role inheritance can become intricate as roles are nested.
-
Dynamic Environment Adaptation : Adapting roles and permissions to rapidly changing environments can be a challenge in dynamic organizations.
Conclusion
Role-Based Access Control is a powerful access management framework that enhances security, simplifies access control, and promotes scalability in organizations. By understanding the principles of RBAC and effectively implementing them, organizations can strengthen their cybersecurity posture, mitigate risks, and ensure regulatory compliance.
Understanding RBAC is essential for organizations looking to establish robust access control mechanisms, safeguard sensitive data, and maintain compliance with industry regulations and standards.
RBAC Permission Inheritance Models
Permission inheritance in Role-Based Access Control (RBAC) allows for the propagation of permissions through a hierarchy of roles. In this blog section, we will delve into the definition and purpose of RBAC Permission Inheritance Models, explore common inheritance models, highlight the advantages of utilizing such models, and provide insights into implementation best practices.
Definition and Purpose: Understanding the Foundation of RBAC Permission Inheritance Models
Role-Based Access Control (RBAC) serves as a fundamental framework for managing permissions within organizations. The concept of permission inheritance within RBAC further refines this framework by elucidating how permissions flow through different levels of roles. By establishing a clear pathway for permission delegation, organizations can effectively streamline access management processes and ensure proper authorization mechanisms.
Common Inheritance Models: Exploring Diverse Approaches
Within RBAC, various inheritance models cater to different organizational structures and requirements. Some common inheritance models include: 1. Flat Inheritance: Direct assignment of permissions to roles without any hierarchical delegation. 2. Role Hierarchy: Cascading of permissions from superior roles to subordinates, creating a structured permission flow to maintain organizational hierarchy. 3. Constraint-Based Inheritance: Permissions inheritance based on predefined constraints or conditions, allowing for more nuanced control over access rights. 4. Mandatory Access Control (MAC): A model where access rights are determined by a central authority, often used in high-security environments.
Advantages of Utilizing Inheritance Models: Leveraging Operational Efficiency
The adoption of RBAC Permission Inheritance Models presents numerous advantages: 1. Simplicity in Management: Reduced complexity in permission administration due to streamlined inheritance mechanisms, leading to more efficient access control processes. 2. Enhanced Scalability: Facilitated permission assignment scalability as organizational roles evolve and grow in complexity. 3. Ensured Consistency: Enforcement of uniform permission application across roles, promoting compliance, and enhancing security measures. 4. Granular Control: Fine-tuning of permissions at various levels to meet specific organizational needs and ensure precise access management. 5. Improved Auditability: Enhanced tracking and auditing capabilities for permissions, aiding in regulatory compliance and security assessments.
Implementation Best Practices: Optimizing RBAC Inheritance
To maximize the benefits of RBAC Permission Inheritance Models, organizations should consider implementing best practices such as periodic role reviews, documentation of inheritance rules, regular security audits, role-based training for employees, and continuous monitoring of access control policies. By integrating these practices, organizations can maintain a robust access control environment that aligns with their evolving operational requirements and security standards.
By embracing the nuances of RBAC Permission Inheritance Models and adopting tailored strategies for implementation, organizations can bolster their security posture and operational efficiency in managing access rights effectively and securely.
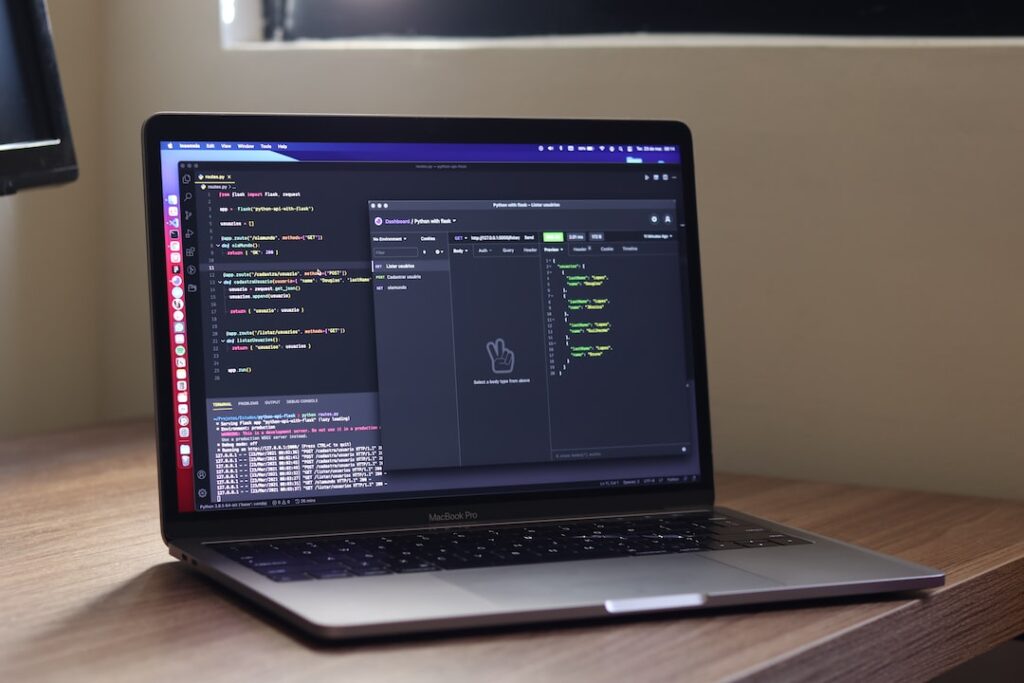
Implementing RBAC Models for Secure Access
Best Practices for Implementation
Role-Based Access Control (RBAC) models are an essential part of ensuring secure access control within organizations. To implement RBAC effectively, there are several best practices to consider:.
-
Clearly Define Roles : Start by clearly defining roles within your organization and assign specific permissions to each role based on job responsibilities.
-
Regularly Review and Update Roles : As your organization grows and changes, it’s crucial to regularly review and update roles to ensure they align with current job functions.
-
Limit Access : Follow the principle of least privilege by granting employees the minimum level of access they need to perform their job tasks.
-
Implement Role Hierarchies : Establish role hierarchies to streamline the assignment of permissions and ensure proper access control.
Challenges Faced and Solutions
While implementing RBAC models, organizations often encounter various challenges. Some common challenges include:.
-
Role Proliferation : The creation of numerous roles can lead to complexity and difficulties in managing permissions.
-
Role Inflation : Over time, roles may accumulate unnecessary permissions, leading to security risks.
-
Role Mapping : Mapping user roles to job functions accurately can be a complex task.
To address these challenges, organizations can consider the following solutions:.
-
Regular Auditing : Conduct regular audits to identify obsolete roles and permissions.
-
Automated Role Assignment : Utilize automation tools to streamline role assignment processes and reduce errors.
-
Training and Awareness : Provide training to employees on the importance of role-based access control and how to adhere to security protocols.
Case Studies of Successful Implementation
Several organizations have successfully implemented RBAC models to enhance their access control and security measures. For example:.
-
Company X : Implemented RBAC to streamline access permissions across departments, resulting in improved data security and reduced unauthorized access incidents.
-
Organization Y : Utilized RBAC to enforce strict access control policies, leading to enhanced compliance with regulatory requirements and data protection standards.
-
Enterprise Z : Integrated RBAC into their cybersecurity framework, resulting in a significant decrease in security breaches and data leaks.
By studying these case studies, organizations can gain valuable insights into the benefits and outcomes of implementing RBAC models for secure access control.
Ensuring Security in Permission Inheritance
Role of Auditing and Monitoring
In the realm of permission inheritance, maintaining a robust security posture is paramount. Auditing and monitoring play a pivotal role in fortifying the integrity of access controls. By instituting stringent auditing procedures and closely monitoring user activities and permission changes, organizations can swiftly detect and respond to any unauthorized access attempts or suspicious behavior. This proactive approach not only bolsters security defenses but also ensures that access rights are allocated judiciously to the appropriate individuals. Regular audits not only identify potential vulnerabilities but also serve as a proactive measure to prevent security incidents, showcasing a commitment to data protection and compliance.
Regular Reviews and Updates
Continual vigilance is essential in the realm of access controls. Regular reviews and updates of permission settings are imperative to adapt to the evolving landscape of organizational dynamics. As businesses grow and personnel transitions occur, a periodic reassessment of access permissions is necessary. This iterative process helps in purging obsolete permissions, reducing the likelihood of data breaches, and aligning access privileges with the current operational requirements. Moreover, scheduled reviews provide an opportunity to enhance security protocols, implement new technologies, and reinforce the organization’s overall security posture.
Potential Risks and Mitigation Strategies
Comprehending the potential vulnerabilities inherent in permission inheritance is fundamental to crafting effective mitigation tactics. Common risks include the exploitation of inherited permissions, unauthorized access stemming from misconfigurations, and vulnerabilities within the inheritance mechanism. To counter these threats, organizations can implement a multifaceted approach encompassing principles like least privilege access, recurrent security education for staff, the adoption of multi-factor authentication mechanisms, and the encryption of sensitive data at rest and in transit. Additionally, conducting regular penetration testing and vulnerability assessments can proactively identify weaknesses in the permission inheritance model, allowing for timely remediation actions and security enhancements.
By proactively recognizing and mitigating these risks, entities can elevate the security stature of their permission inheritance framework and shield sensitive data from unauthorized intrusions. Embracing a security-first mindset and adhering to best practices in access control management are indispensable in safeguarding organizational assets and preserving data integrity. Continuous improvement in security measures, coupled with a commitment to staying abreast of emerging threats and security trends, is essential for maintaining a resilient permission inheritance environment that upholds confidentiality, integrity, and availability of critical data.
Conclusion
Streamlining Role-Based Access Control (RBAC) permission inheritance models is crucial for ensuring secure access control within an organization. By carefully designing and implementing RBAC models that adhere to best practices, organizations can effectively manage permissions, reduce the risk of unauthorized access, and enhance overall security posture. It is essential for organizations to continuously evaluate and refine their RBAC models to adapt to evolving security threats and business needs, ultimately safeguarding sensitive data and resources from potential breaches and unauthorized activities.