Hybrid Cloud Security: Strategies and Best Practices

Businesses are increasingly adopting hybrid cloud environments to leverage the benefits of both public and private cloud services. However, with this transition comes the critical need for robust security measures to protect sensitive data and ensure compliance with regulations. Achieving hybrid cloud security requires effective configurations that seamlessly integrate security protocols across all cloud platforms. This includes implementing strong encryption methods, access controls, regular monitoring, and incident response plans. By prioritizing security configurations, organizations can fortify their hybrid cloud infrastructure against cyber threats and data breaches. In this context, understanding the nuances of hybrid cloud security and implementing best practices is essential for safeguarding valuable assets in the cloud while maintaining operational efficiency. This article explores key strategies and considerations for achieving hybrid cloud security through effective configurations.
Understanding Hybrid Cloud Security
Benefits of Hybrid Cloud
- Enhanced Flexibility and Scalability
- Cost-Effectiveness and Resource Optimization
- Improved Redundancy and Disaster Recovery Strategies
- Seamless Data Migration and Hybrid Architecture Management
- Hybrid Cloud Security Best Practices
Security Challenges in Hybrid Cloud Environments
- Data Security and Privacy Concerns
- Regulatory Compliance and Governance Risks
- Integration and Interoperability Challenges
- Identity and Access Management Complexity
- Mitigating Security Risks in Hybrid Cloud Environments
As organizations increasingly adopt hybrid cloud infrastructures to leverage the benefits of both public and private clouds, understanding hybrid cloud security becomes paramount. The benefits of hybrid cloud include enhanced flexibility and scalability, cost-effectiveness, improved redundancy, disaster recovery strategies, seamless data migration, and efficient hybrid architecture management. Additionally, implementing hybrid cloud security best practices is vital to ensure data protection and regulatory compliance.
However, along with these advantages, organizations face various security challenges in hybrid cloud environments. Data security and privacy concerns arise due to the distributed nature of data across multiple cloud environments, making it crucial to implement robust encryption, data masking, and access control measures. Regulatory compliance and governance risks also pose challenges as organizations must adhere to industry regulations, certifications, and data protection laws across different cloud platforms.
Moreover, integration and interoperability challenges can hinder the seamless operation of hybrid cloud environments, requiring advanced integration solutions, API management, and standardized protocols. Identity and access management complexity further complicates security, necessitating comprehensive authentication, multi-factor authentication, and authorization mechanisms to safeguard data and resources effectively.
Mitigating security risks in hybrid cloud environments involves continuous monitoring, threat detection, incident response planning, and security testing to proactively identify and address vulnerabilities. Implementing security controls, encryption key management, and security automation tools are essential components of a robust hybrid cloud security strategy.
While hybrid cloud offers numerous benefits, addressing security challenges through proactive measures, continuous monitoring, and strategic planning is essential for maintaining a secure hybrid cloud environment and ensuring data confidentiality, integrity, and availability.
Key Components of Hybrid Cloud Security Configurations
Hybrid cloud environments have gained immense popularity in recent years due to their flexibility, scalability, and cost-effectiveness. As organizations increasingly adopt hybrid cloud models to leverage the benefits of both on-premises infrastructure and cloud services, ensuring robust security measures becomes paramount to safeguard sensitive data and uphold regulatory compliance. In this comprehensive guide, we will delve deeper into the key components of hybrid cloud security configurations that organizations must prioritize to fortify their defenses.
-
Encryption and Key Management: Safeguarding data in transit and at rest is a fundamental aspect of hybrid cloud security. Encryption serves as a critical safeguard, ensuring that data remains unintelligible to unauthorized entities. Implementing robust encryption algorithms and effective key management strategies is imperative to thwart potential cyber threats and data breaches. Additionally, organizations should consider the use of encryption technologies such as Advanced Encryption Standard (AES) to enhance data protection. Encryption not only protects data confidentiality but also ensures data integrity and authenticity throughout its lifecycle.
-
Identity and Access Management (IAM): Managing user identities and controlling access to resources are vital aspects of hybrid cloud security. By implementing stringent IAM policies, organizations can authenticate and authorize users, devices, and applications accessing their cloud infrastructure. Employing multi-factor authentication, role-based access controls, and continuous monitoring mechanisms can bolster IAM practices and mitigate the risk of unauthorized access. Furthermore, integrating IAM solutions with identity federation protocols like Security Assertion Markup Language (SAML) can enable seamless and secure access across hybrid cloud environments.
-
Network Security Protocols: Securing network communications within a hybrid cloud environment is essential to prevent unauthorized access and data interception. Implementing robust network security protocols such as Virtual Private Networks (VPNs), Transport Layer Security (TLS), and firewall solutions can help create secure communication channels and protect sensitive data from malicious activities. Additionally, deploying intrusion detection and prevention systems can enhance threat detection capabilities and proactively defend against cyber threats. Continuous monitoring of network traffic, coupled with regular security updates and patches, is crucial to maintaining a secure network environment in a hybrid cloud setup.
By focusing on these essential components of hybrid cloud security configurations, organizations can establish a resilient security posture and navigate the complexities of operating in a hybrid cloud environment. Embracing a proactive security approach, regular security audits, and staying abreast of emerging security trends are crucial steps to safeguarding critical data assets and maintaining trust in hybrid cloud deployments. Investing in employee training programs and fostering a culture of security awareness can further fortify an organization’s overall security strategy in the ever-evolving hybrid cloud landscape.
Best Practices for Implementing Hybrid Cloud Security Configurations
Regular Security Audits
Regular security audits are essential for maintaining the security of hybrid cloud environments. Conducting regular audits helps in identifying vulnerabilities, misconfigurations, and potential security threats. It ensures that security measures are up to date and effective. Audits should encompass not only the cloud infrastructure but also applications, data storage, and network configurations. Additionally, penetration testing can be beneficial to assess the effectiveness of security controls and identify any weak points that attackers could exploit.
Data Classification and Protection Strategies
Implementing data classification and protection strategies is crucial for safeguarding sensitive information in hybrid cloud setups. By categorizing data based on its sensitivity, organizations can apply appropriate security controls and encryption mechanisms to protect it from unauthorized access or data breaches. Data classification should consider regulatory compliance requirements and industry standards. Organizations should also regularly review and update their data classification policies to adapt to evolving threats and business needs.
Incident Response Planning
Having a well-defined incident response plan is a key aspect of hybrid cloud security. In the event of a security incident or data breach, organizations need to have clear guidelines and procedures in place to detect, respond to, and recover from such incidents. A robust incident response plan minimizes the impact of security breaches and enables quick restoration of services. Organizations should conduct regular tabletop exercises to test the effectiveness of their incident response procedures and ensure that all stakeholders are familiar with their roles and responsibilities during a security incident.
Employee Training and Awareness
Employee training and awareness programs play a vital role in strengthening hybrid cloud security. Employees should be educated on best practices for data security, the risks associated with cloud computing, and how to identify and report security incidents. Security awareness training should be an ongoing initiative to reinforce security policies and promote a culture of security within the organization.
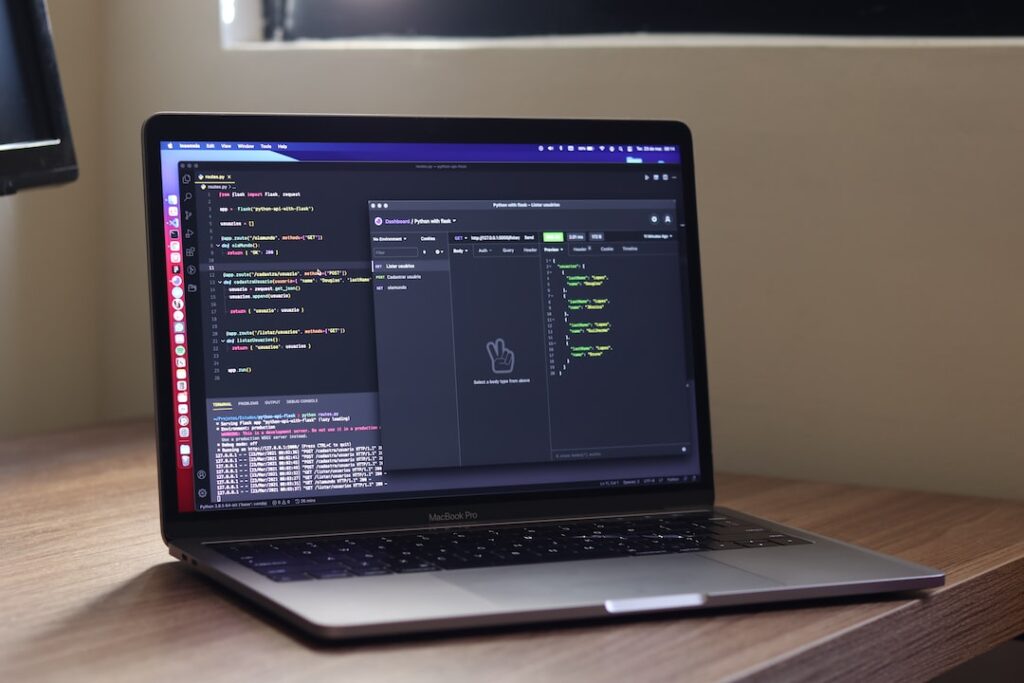
Continuous Monitoring and Threat Intelligence
Continuous monitoring of hybrid cloud environments is essential for detecting and mitigating security threats in real time. By implementing security information and event management (SIEM) solutions, organizations can gain visibility into their cloud infrastructure, monitor for suspicious activities, and respond promptly to potential security incidents. Additionally, leveraging threat intelligence feeds can provide valuable insights into emerging threats and proactive measures to enhance security posture.
Implementing robust security practices in hybrid cloud environments is critical to safeguarding data, maintaining compliance, and protecting against evolving cyber threats. By following the best practices outlined above and staying informed about the latest security trends, organizations can strengthen their security posture and ensure the integrity and confidentiality of their data in the hybrid cloud.
Section: Case Studies: Successful Hybrid Cloud Security Implementations
In this blog section, we will delve into two compelling case studies showcasing successful implementations of hybrid cloud security strategies. Let’s explore how Company A and Company B effectively secured their operations through different approaches.
Company A: Secure Migration to Hybrid Cloud
Overview:
Company A, a leading tech firm, successfully migrated to a hybrid cloud environment while ensuring robust security measures.
Key Points:
-
Risk Assessment and Planning : Company A conducted a thorough risk assessment before migrating to identify potential security gaps.
-
Data Encryption and Access Control : Implementing encryption protocols and strict access control policies ensured data security in transit and at rest.
-
Continuous Monitoring : Utilizing advanced monitoring tools enabled real-time threat detection and incident response.
-
Employee Training : Company A invested in training programs to educate employees on best security practices in the hybrid cloud environment.
Additional Insights : Company A’s journey towards a secure hybrid cloud involved collaboration with cloud service providers to ensure data sovereignty and compliance with industry regulations. The implementation of a robust incident response plan further fortified their security posture, enabling swift mitigation of potential threats.
Company B: Enhanced Security Through Configuration Optimization
Overview:
Company B, a financial institution, enhanced its security posture by optimizing configurations in the hybrid cloud infrastructure.
Key Points:
-
Automated Compliance Checks : Company B automated compliance checks to ensure configurations align with industry standards and regulations.
-
Multi-Factor Authentication (MFA) : Implementing MFA across all systems added an extra layer of security and mitigated unauthorized access.
-
Regular Audits and Penetration Testing : Conducting regular audits and penetration tests helped Company B identify and remediate vulnerabilities proactively.
-
Collaboration with Security Experts : Collaborating with external security experts provided valuable insights and recommendations for continuous improvement.
Additional Insights : Company B’s success in hybrid cloud security was further bolstered by the implementation of a secure DevOps culture, where security was integrated into every stage of development. This proactive approach not only enhanced security but also fostered innovation within the organization.
By examining these case studies, organizations can gain valuable insights into implementing effective hybrid cloud security strategies. These success stories highlight the importance of proactive security measures, employee training, and collaboration with industry experts in ensuring a robust security posture in the hybrid cloud environment. Stay tuned for more success stories and best practices in cloud security!.
Conclusion
Achieving hybrid cloud security with effective configurations is crucial in today’s digital landscape. By implementing strong security measures, such as encryption, access controls, and monitoring, organizations can protect their sensitive data and ensure compliance with regulations. Additionally, regular security audits and updates are essential to stay ahead of potential threats. With a proactive approach and a focus on continuous improvement, businesses can confidently leverage the benefits of hybrid cloud environments while maintaining a robust security posture.